Latest news from the anti-virus industry provided by independent anti-virus advisors, Virus Bulletin
NewsUS and UK spam legislation in place Anti-spam legislation in place. 29 December 2003Number crunchingCalculating the average cost of a virus attack - estimates or guesstimates?… https://www.virusbulletin.com/blog/2003/
It's that time of year again when we're frantically scouring the shopping malls for something unique and meaningful to give to our loved ones. Coincidentally, it's also that time of year when VB turns out its stock cupboards and puts some truly fabulous m…
It's that time of year again when we're frantically scouring the shopping malls for something unique and meaningful to give to our loved ones. Coincidentally, it's also that time… https://www.virusbulletin.com/blog/2002/12/stocking-fillers/
We examine ViraLock, a product which promises 'Zero Escape For Email Viruses', provided, it seems, the virus plays by their rules.
We examine ViraLock, a product which promises 'Zero Escape For Email Viruses', provided, it seems, the virus plays by their rules. It's understandable that we greet announcements… https://www.virusbulletin.com/blog/2002/11/some-thoughts-viralock/
New security portal unveiled by publishers of Information Security Bulletin magazine.
New security portal unveiled by publishers of Information Security Bulletin magazine. Last month a new security portal was unveiled by the publishers of Information Security… https://www.virusbulletin.com/blog/2002/11/who-s-there/
McAfee Security issues press release estimating the potential costs to businesses of 'the next big virus attack'
McAfee Security issues press release estimating the potential costs to businesses of 'the next big virus attack' McAfee Security has become the latest security company to issue a… https://www.virusbulletin.com/blog/2002/11/paying-price/
A British man has appeared in court charged with the creation and distribution of a trio of mass-mailing viruses: Gokar, Redesi and Admirer.
A British man has appeared in court charged with the creation and distribution of a trio of mass-mailing viruses: Gokar, Redesi and Admirer. A British man has appeared in court… https://www.virusbulletin.com/blog/2002/11/writer-virus-trio-court/
Reports are that Jan de Wit, author of the 'Kournikova' virus (VBSWG variant) has lost his appeal against 150 hours of community service.
Reports are that Jan de Wit, author of the 'Kournikova' virus (VBSWG variant) has lost his appeal against 150 hours of community service. The Register reports that Jan de Wit,… https://www.virusbulletin.com/blog/2002/10/kournikova-writer-loses-appeal/
A nuisance email which is neither viral nor a hoax is proving to be equally bothersome.
A nuisance email which is neither viral nor a hoax is proving to be equally bothersome. A nuisance email which is neither viral nor a hoax is proving to be equally bothersome.… https://www.virusbulletin.com/blog/2002/10/friends-these/
A warning issued by Israeli security firm GreyMagic Software last month revealed a total of nine vulnerabilities in IE 5.5 and 6.0, all concerning object caching.
A warning issued by Israeli security firm GreyMagic Software last month revealed a total of nine vulnerabilities in IE 5.5 and 6.0, all concerning object caching. A warning… https://www.virusbulletin.com/blog/2002/10/moth-eaten-software/
So confident is Trend Micro of its virus detection abilities that it is offering a financial penalty-backed detection guarantee.
So confident is Trend Micro of its virus detection abilities that it is offering a financial penalty-backed detection guarantee. So confident is Trend Micro of its virus detection… https://www.virusbulletin.com/blog/2002/10/service-or-bust/
Just occasionally, a virus infection can have some positive effects...
Just occasionally, a virus infection can have some positive effects... Much like biological viruses, it turns out that infections by computer viruses can lead to increased measures… https://www.virusbulletin.com/blog/2002/09/viruses-some-good/
The latest award for the most tenuous product-pushing story goes to BitDefender, whose marketeers claim a 'mosquito-borne disease could easily become a computer infection.'
The latest award for the most tenuous product-pushing story goes to BitDefender, whose marketeers claim a 'mosquito-borne disease could easily become a computer infection.' The… https://www.virusbulletin.com/blog/2002/09/bring-deet/
The Infosecurity show and exhibition has gone virtual with the launch of the first Infosecurity World Online exhibition. But where are the sweets?
The Infosecurity show and exhibition has gone virtual with the launch of the first Infosecurity World Online exhibition. But where are the sweets? The Infosecurity show and… https://www.virusbulletin.com/blog/2002/09/virtually-there/
 In 1994, along with the Olympic Games came an Olympic virus, from a group of Swedish virus authors calling themselves ‘Immortal Riot’. We look back at Mikko Hyppönen's analysis in the VB archive.
In 1994, along with the Olympic Games came an Olympic virus, from a group of Swedish virus authors calling themselves ‘Immortal Riot’. We look back at Mikko Hyppönen's analysis in the VB archive.
 Announcing the VB2016 call for last-minute papers and a number of discounts on the conference registration rate.
Announcing the VB2016 call for last-minute papers and a number of discounts on the conference registration rate.
 The website of the Carol Davila University of Medicine and Pharmacy has been compromised to inject a hidden iframe into the site's source code that serves the Neutrino exploit kit and may infect visitors with ransomware.
The website of the Carol Davila University of Medicine and Pharmacy has been compromised to inject a hidden iframe into the site's source code that serves the Neutrino exploit kit and may infect visitors with ransomware.
 While there are no actually risks involved in using MD5s in malware analyses, it reinforces bad habits and we should all start using SHA-256 instead.
While there are no actually risks involved in using MD5s in malware analyses, it reinforces bad habits and we should all start using SHA-256 instead.
 In 2001, ‘Code Red’ caused White House administrators to change the IP address of the official White House website, and even penetrated Microsoft’s own IIS servers.
In 2001, ‘Code Red’ caused White House administrators to change the IP address of the official White House website, and even penetrated Microsoft’s own IIS servers.
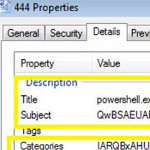 A new paper by FireEye researcher Ankit Anubhav provides an overview of evasion techniques applied by recently discovered malware.
A new paper by FireEye researcher Ankit Anubhav provides an overview of evasion techniques applied by recently discovered malware.
 Recently, ESET researchers uncovered a new espionage toolkit targeting targeting Central and Eastern Europe. They provide some details in a guest post.
Recently, ESET researchers uncovered a new espionage toolkit targeting targeting Central and Eastern Europe. They provide some details in a guest post.
 Anti-virus vendor Avast has announced the acquisition of its rival AVG for 1.3 billion US dollars.
Anti-virus vendor Avast has announced the acquisition of its rival AVG for 1.3 billion US dollars.
 Passwords have long been a weak point in the security chain, despite efforts to encourage users to pick strong ones. 13 years ago, Martin Overton wrote an article highlighting the weakness and explaining why it is the human element that presents the biggest risk to computer security - something that rings as true today as it did 13 years ago.
Passwords have long been a weak point in the security chain, despite efforts to encourage users to pick strong ones. 13 years ago, Martin Overton wrote an article highlighting the weakness and explaining why it is the human element that presents the biggest risk to computer security - something that rings as true today as it did 13 years ago.