Posted by Virus Bulletin on Feb 10, 2015
Fabio Assolini explains how cybercriminals are targeting boletos.
Since the close of the VB2014 conference in Seattle in October, we have been sharing VB2014 conference papers as well as video recordings of the presentations. Today, we have added 'P0wned by a barcode: stealing money from offline users' by Kaspersky Lab researcher Fabio Assolini.
If you aren't from Brazil, chances are you'll have never heard of the 'boleto bancário'. Yet boletos (as they are usually known) are a common way to pay bills in the country. At ATMs, banks and many shops, the unique barcode on your printed boleto allows you to pay a utility bill or a bill for online shopping, even if you don't have an online bank account.
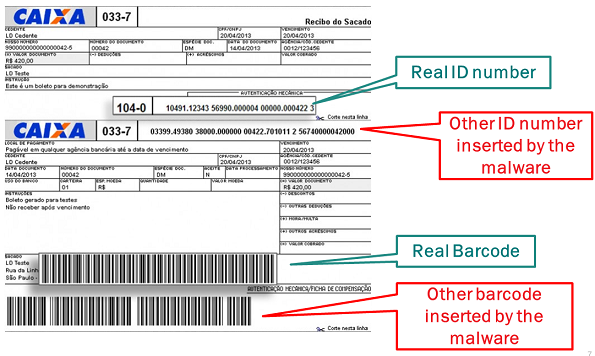
For this to work well, it is important that no one is able to tamper with the barcode. Yet that is exactly what has been happening: Brazilian citizens have been targeted by malware that modifies boletos as they are being downloaded, making their barcodes point to different bank accounts from those the user believes they are paying into - accounts that are controlled by the criminals.
Boleto fraud continues to be a problem. Yesterday, security firm RSA published a blog post highlighting a case in which malicious JavaScript is being injected into banking websites through DNS poisoning. (If accurate, this suggests the affected banks' security is well below par; HTTPS should make such attacks impossible.)
Though boletos are unique to Brazil, similar payment systems are used in other countries. At the most recent Botconf conference, Łukasz Siewierski discussed malware that targets Polish bank account holders by replacing account numbers stored in the clipboard.
You can read Fabio Assolini's paper on boletos here in HTML-format, or download it here as a PDF (no registration or subscription required). You can download the presentation slides here. We have also uploaded the presentation to our YouTube channel.
Fabio has spoken on cybercrime in Brazil at various VB conferences. We also recommend watching the video of his VB2013 presentation on malicious PAC files.
Posted on 10 February 2015 by Martijn Grooten