Posted by Martijn Grooten on May 8, 2018
 Registration for VB2018, the 28th International Virus Bulletin conference, is now open, with an early bird rate available until 1 July.
Registration for VB2018, the 28th International Virus Bulletin conference, is now open, with an early bird rate available until 1 July.
Posted by Martijn Grooten on May 1, 2018
 In April, VB's Martijn Grooten attended the RSA Expo in San Francisco. He shares his views on the expo and the industry.
In April, VB's Martijn Grooten attended the RSA Expo in San Francisco. He shares his views on the expo and the industry.
Posted by Martijn Grooten on Apr 30, 2018
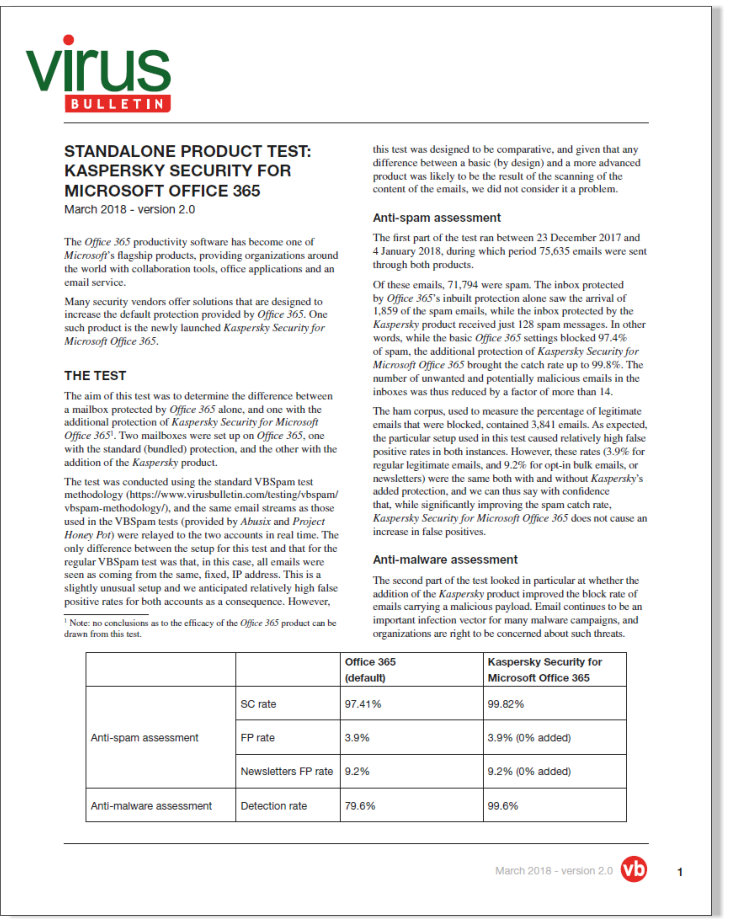 There are a number of security solutions on the market that are designed to increase the default protection provided by Office 365. One such product is the newly launched Kaspersky Security for Microsoft Office 365. Virus Bulletin was commissioned to measure the effectiveness of the Kaspersky product compared to the Office 365 baseline protection.
There are a number of security solutions on the market that are designed to increase the default protection provided by Office 365. One such product is the newly launched Kaspersky Security for Microsoft Office 365. Virus Bulletin was commissioned to measure the effectiveness of the Kaspersky product compared to the Office 365 baseline protection.
Posted by Martijn Grooten on Apr 27, 2018
 The GravityRAT malware, discovered by Cisco Talos researchers, gives some interesting insight into modern malware development.
The GravityRAT malware, discovered by Cisco Talos researchers, gives some interesting insight into modern malware development.
Posted by Martijn Grooten on Apr 25, 2018
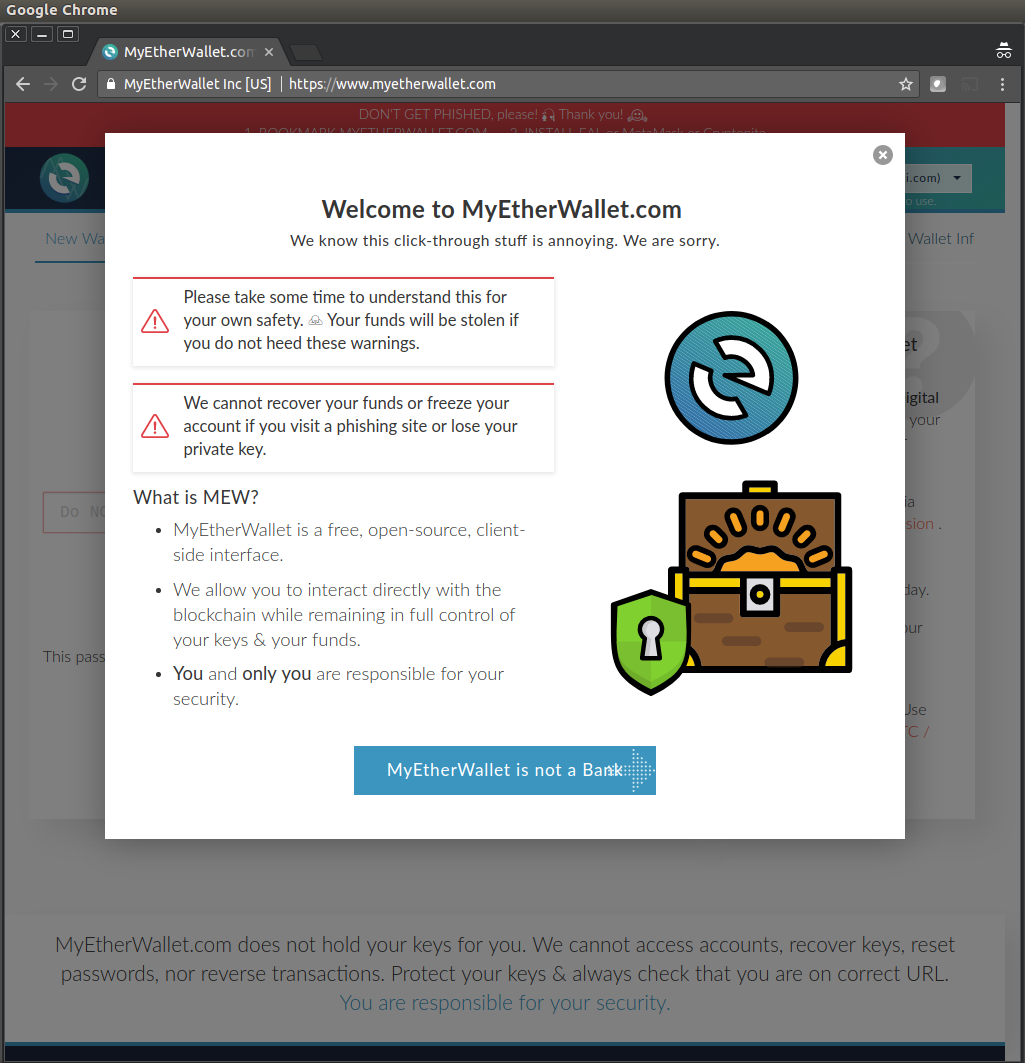 A BGP hijack was used to take over some of Amazon's DNS infrastructure, which was then used to serve a phishing site to users of the MyEtherWallet service.
A BGP hijack was used to take over some of Amazon's DNS infrastructure, which was then used to serve a phishing site to users of the MyEtherWallet service.
Posted by Martijn Grooten on Apr 24, 2018
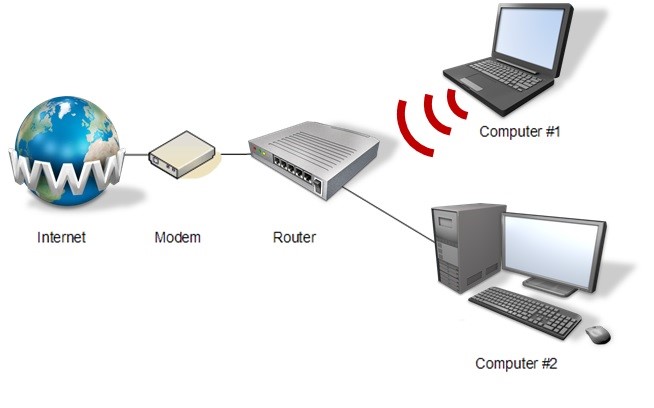 Various security companies are offering security-focused routers. This is a good trend and may help mitigate a lot of the issues that come with the IoT.
Various security companies are offering security-focused routers. This is a good trend and may help mitigate a lot of the issues that come with the IoT.
Posted by Virus Bulletin on Apr 23, 2018
 Most of the switch from IPv4 to IPv6 will happen seamlessly. But we cannot assume it won't introduce new security issues.
Most of the switch from IPv4 to IPv6 will happen seamlessly. But we cannot assume it won't introduce new security issues.
Posted by Martijn Grooten on Apr 19, 2018
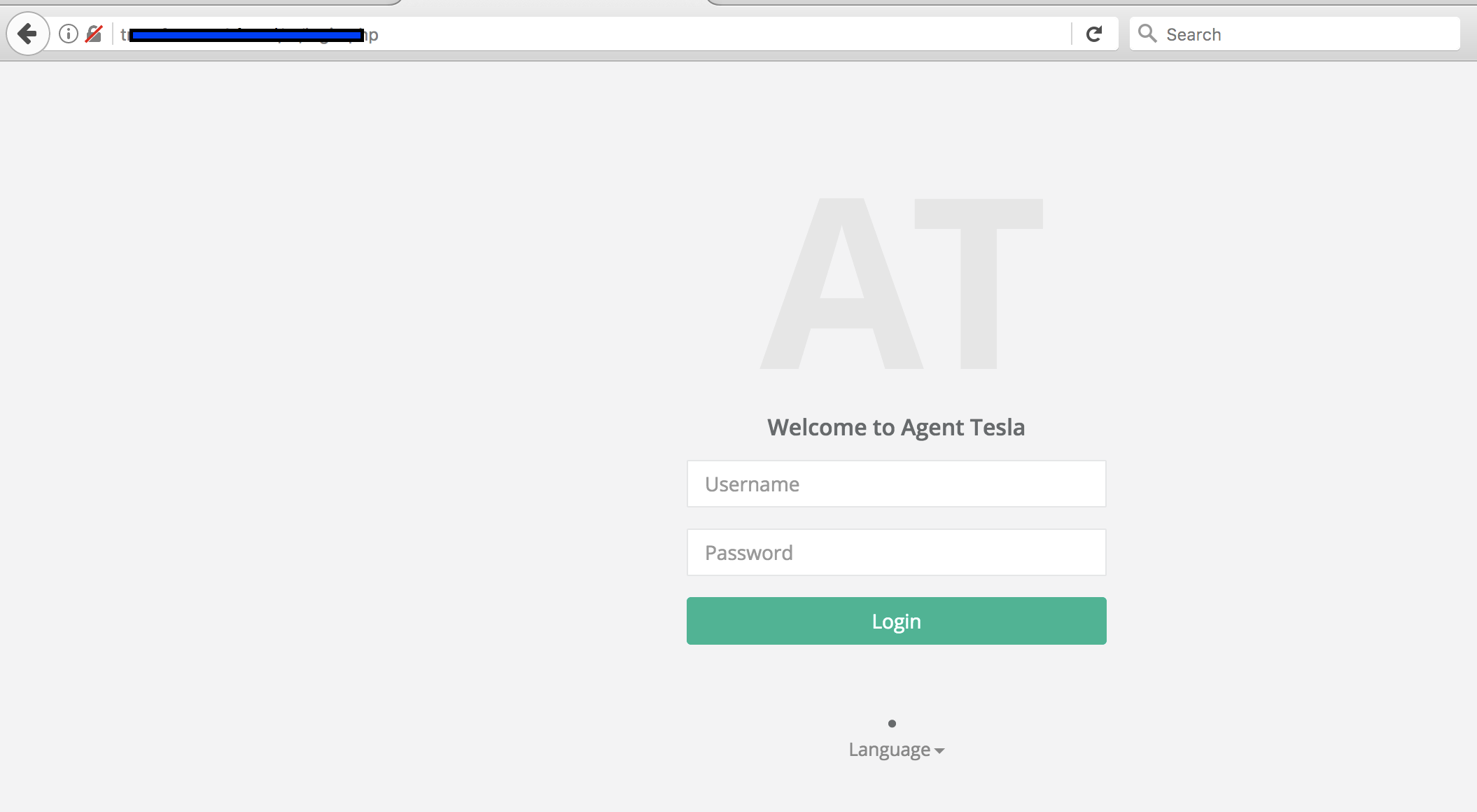 Since their return four years ago, Office macros have been one of the most common ways to spread malware. Today, we publish a research paper which looks in detail at a campaign in which VBA macros are used to execute PowerShell code, which in turn downloads the Tesla information-stealing trojan.
Since their return four years ago, Office macros have been one of the most common ways to spread malware. Today, we publish a research paper which looks in detail at a campaign in which VBA macros are used to execute PowerShell code, which in turn downloads the Tesla information-stealing trojan.
Posted by Martijn Grooten on Apr 18, 2018
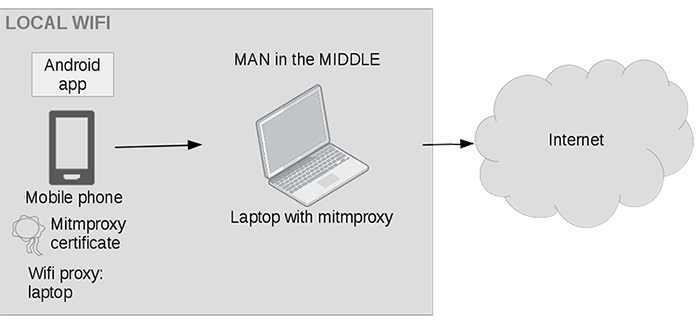 Within a few years, Android malware has grown from a relatively small threat to a huge problem involving more than three million new malware samples a year. Axelle Apvrille, one of the world's leading Android malware researchers, will deliver a workshop on Android reverse engineering at VB2018 in Montreal this October. Last year, Axelle presented a paper at VB2017 on some of the less common tools that can be used to reverse engineer Android malware. Today, we publish both the paper and the recording of Axelle's presentation.
Within a few years, Android malware has grown from a relatively small threat to a huge problem involving more than three million new malware samples a year. Axelle Apvrille, one of the world's leading Android malware researchers, will deliver a workshop on Android reverse engineering at VB2018 in Montreal this October. Last year, Axelle presented a paper at VB2017 on some of the less common tools that can be used to reverse engineer Android malware. Today, we publish both the paper and the recording of Axelle's presentation.
Posted by Martijn Grooten on Apr 16, 2018
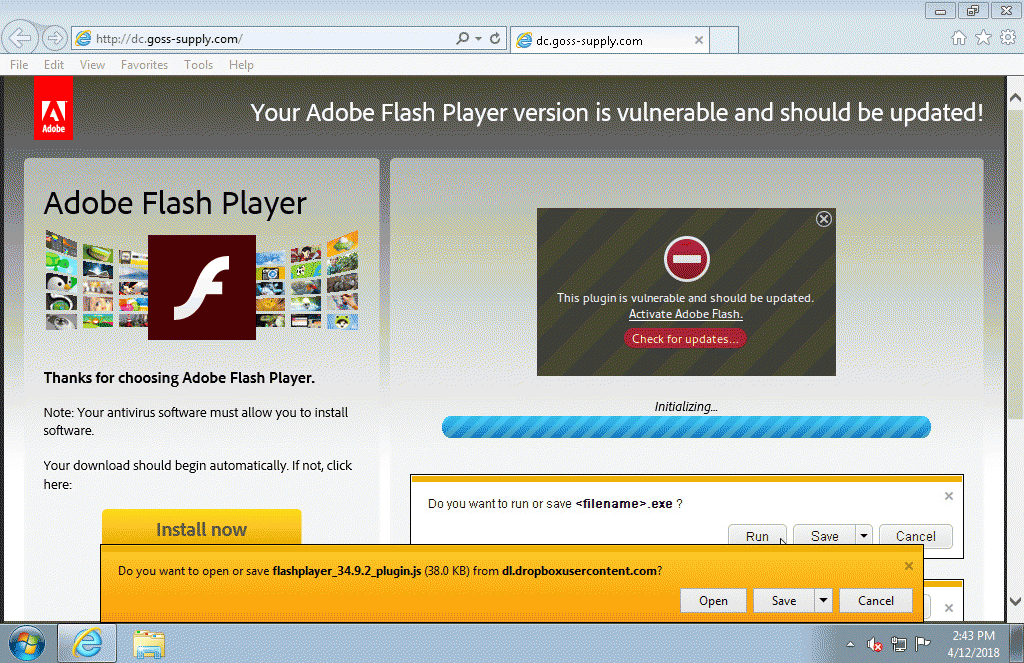 Compromised websites are being used to serve fake Flash Player uploads that come with a malicious payload.
Compromised websites are being used to serve fake Flash Player uploads that come with a malicious payload.