The GandCrab ransomware regularly updated itself to newer versions to stay ahead of decryptors released by security researchers, and regularly included taunts, jokes and references to security organizations in its code. In a new paper, the AhnLab Security…
For more details of GandCrab, also see the VB2019 paper and presentation by McAfee researchers John Fokker and Alexandre Mundo, who looked both at the malware code and its… https://www.virusbulletin.com/blog/2020/01/new-paper-behind-scenes-gandcrabs-operation/
With the VB2020 Call for Papers now open, we explain how the selection procedure works, which may help you during your abstract submission.
We recently opened the call for papers for VB2020, which is to take place 30 September to 2 October in Dublin, Ireland. The deadline for the call for papers is Sunday 15 March.… https://www.virusbulletin.com/blog/2020/01/vb2020-call-papers/
In 2019 we saw a rise in the number of targeted malware infections spread via ISPs and service providers. In a last-minute paper presented at VB2019 in London, Kaspersky researcher Denis Legezo discussed the details of a number of such cases. Today we rel…
In 2019 we saw an increase in the number of targeted malware infections spread via ISPs and service providers. Some notable cases included the installation of digital certificates… https://www.virusbulletin.com/blog/2020/01/vb2019-presentation-targeted-attacks-through-isps/
In a last-minute presentation at VB2019 in London, John Bambenek of the University of Illinois at Urbana-Champaign discussed details of campaigns that used advanced iOS and Android exploit chains against China’s Uighur minority. Today we release the recor…
One of the biggest security stories of 2019 was the use of advanced iOS and Android exploit chains against China’s Uighur minority, first uncovered by Google’s Project Zero with… https://www.virusbulletin.com/blog/2020/01/vb2019-presentation-deep-dive-iphone-exploit-chains/
In the final of a five-part series of blog posts, departing VB Editor Martijn Grooten argues for more emphasis on the good news in security, especially that which is more subtle.
At the end of this month, I will step down as Editor of Virus Bulletin. Before doing so, I have been sharing some 'parting thoughts' in five blog posts, based on my experience… https://www.virusbulletin.com/blog/2019/12/parting-thoughts-5-bringing-good-news/
In the fourth of a five-part series of blog posts, departing VB Editor Martijn Grooten explains why security researchers should refer to other people's work.
At the end of this month, I will step down as Editor of Virus Bulletin. Before I do so, I will share some 'parting thoughts' in five blog posts, based on my experience working in… https://www.virusbulletin.com/blog/2019/12/parting-thoughts-4-big-picture/
China has long been a hotbed of DDoS activities, and today we publish a VB2019 paper by Intezer researcher Nacho Sanmillan who looked at Chinese threat groups engaged in performing DDoS attacks. We have also uploaded the recording of his presentation.
Exploring the Chinese DDoS landscape
Read the paper (HTML)
Download the paper (PDF)
China has long been a hotbed of DDoS activities, with several groups… https://www.virusbulletin.com/blog/2019/12/vb2019-paper-exploring-chinese-ddos-landscape/
In the third of a five-part series of blog posts, departing VB Editor Martijn Grooten explains why he believes security vendors should take their products' security more seriously.
At the end of this month, I will step down as Editor of Virus Bulletin. Before I do so, I will share some 'parting thoughts' in five blog posts, based on my experience working in… https://www.virusbulletin.com/blog/2019/12/parting-thoughts-3-taking-security-seriously/
In the second of a five-part series of blog posts, departing VB Editor Martijn Grooten explains why he believes cybersecurity professionals need to educate themselves on the complexities of the real-world situations in which security is applied.
At the end of this month, I will step down as Editor of Virus Bulletin. Before I do so, I will share some 'parting thoughts' in five blog posts, based on my experience working in… https://www.virusbulletin.com/blog/2019/12/parting-thoughts-2-need-education-security/
Have you analysed a new online threat? Do you know a new way to defend against such threats? Are you tasked with securing systems and fending off attacks? The call for papers for VB2020 is now open and we want to hear from you!
In the October 1990 edition of Virus Bulletin (pdf), then a printed monthly magazine sent to subscribers around the world by post, the very first Virus Bulletin conference was… https://www.virusbulletin.com/blog/2019/12/vb2020-call-papers-now-open/
 VB2021 localhost presents an exciting opportunity to share your research with an even wider cross section of the IT security community around the world than usual, without having to take time out of your work schedule (or budget) to travel.
VB2021 localhost presents an exciting opportunity to share your research with an even wider cross section of the IT security community around the world than usual, without having to take time out of your work schedule (or budget) to travel.
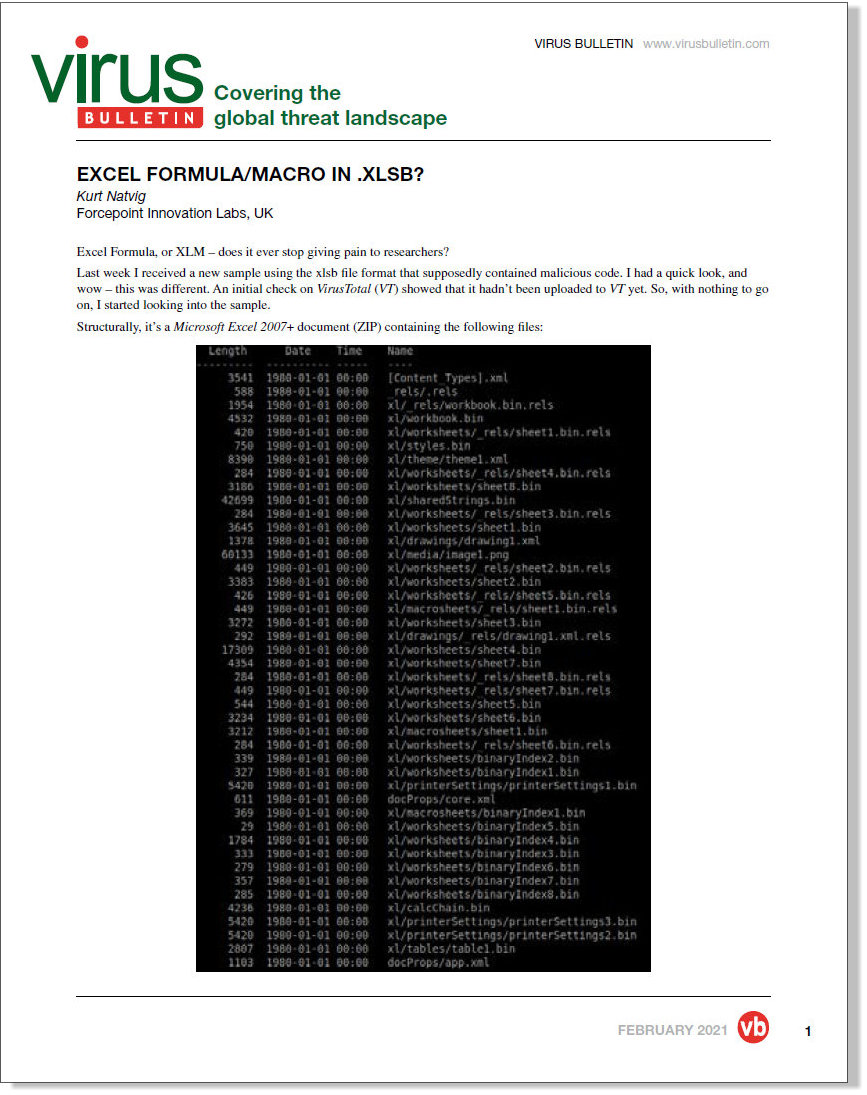 In a follow-up to an article published last week, Kurt Natvig takes us through the analysis of a new malicious sample using the .xlsb file format.
In a follow-up to an article published last week, Kurt Natvig takes us through the analysis of a new malicious sample using the .xlsb file format.
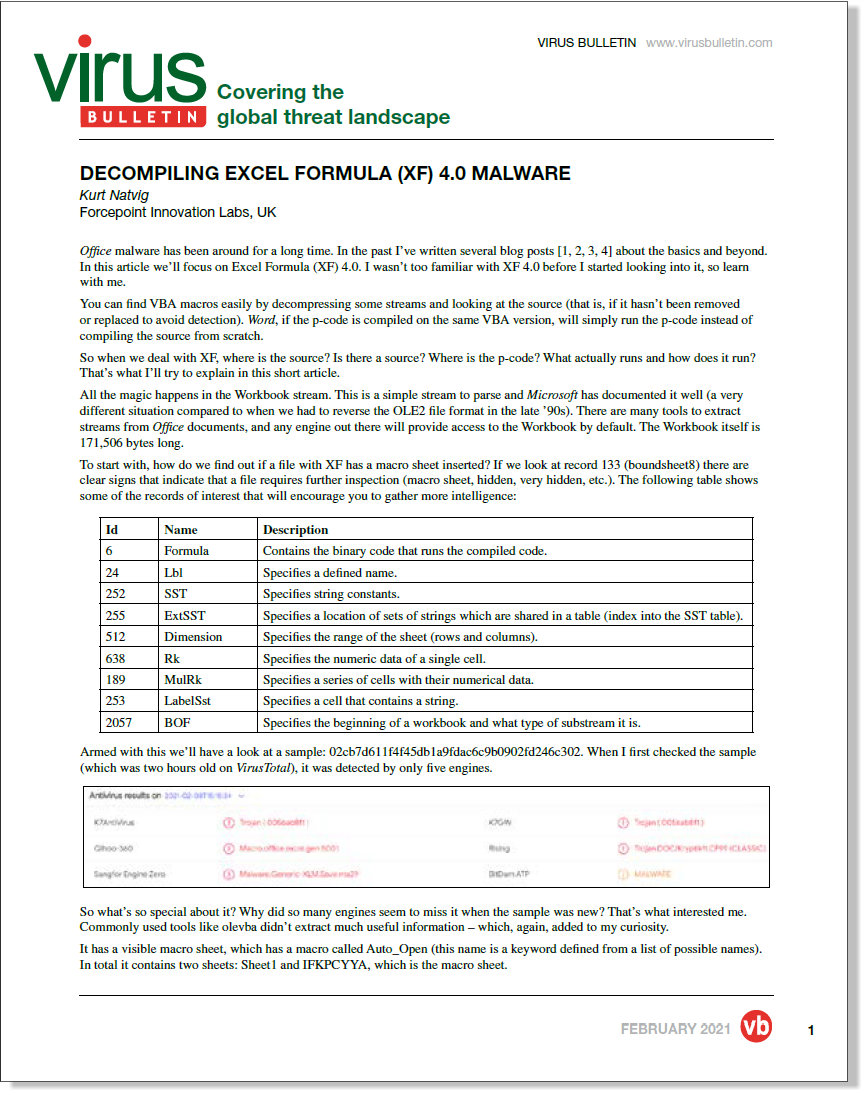 In a new article, researcher Kurt Natvig takes a close look at XF 4.0 malware.
In a new article, researcher Kurt Natvig takes a close look at XF 4.0 malware.
 At VB2019, CSIS researcher Benoît Ancel spoke about a quiet banking trojan actor that has been targeting German users since at least 2014.
At VB2019, CSIS researcher Benoît Ancel spoke about a quiet banking trojan actor that has been targeting German users since at least 2014.
 The call for papers for VB2021 is now open and we want to hear from you - we're planning for flexible presentation formats, so everyone is encouraged to submit, regardless of whether or not you know at this stage whether you'll be able to travel to Prague!
The call for papers for VB2021 is now open and we want to hear from you - we're planning for flexible presentation formats, so everyone is encouraged to submit, regardless of whether or not you know at this stage whether you'll be able to travel to Prague!
 We were very sorry to learn of the passing of researcher Yonathan Klijnsma last week. Here, former VB Editor Martijn Grooten shares his memories of a talented researcher and a very kind person: this month, infosec lost a really good one.
We were very sorry to learn of the passing of researcher Yonathan Klijnsma last week. Here, former VB Editor Martijn Grooten shares his memories of a talented researcher and a very kind person: this month, infosec lost a really good one.
 VB has made all VB2020 localhost presentations available on the VB YouTube channel, so you can now watch - and share - any part of the conference freely and without registration.
VB has made all VB2020 localhost presentations available on the VB YouTube channel, so you can now watch - and share - any part of the conference freely and without registration.
 At VB2020 localhost, threat intelligence consultant Jamie Collier used the analytical technique of backcasting to look at the rise and fall of the cyber threat intelligence industry.
At VB2020 localhost, threat intelligence consultant Jamie Collier used the analytical technique of backcasting to look at the rise and fall of the cyber threat intelligence industry.
 At VB2020 localhost, Carbon Black's Scott Knight presented an approach he and his colleagues have taken to more realistically simulate malware attacks.
At VB2020 localhost, Carbon Black's Scott Knight presented an approach he and his colleagues have taken to more realistically simulate malware attacks.
 At VB2020, researcher Paul Litvak revealed how he put together a comprehensive map of threat actor use of open-source offensive security tools.
At VB2020, researcher Paul Litvak revealed how he put together a comprehensive map of threat actor use of open-source offensive security tools.