Posted by Helen Martin on Feb 5, 2020
With more than 2.5 billion gamers around the world, the video gaming industry has overtaken all other entertainment categories in size and revenue. But in tandem with the boom in video gaming has arisen a growing illegal economy: that of video game cheats and hacks.
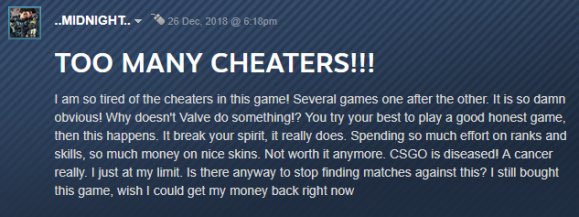 Gaming communities are riddled with messages complaining about the increasing number of cheaters ruining the game for players and the reputation of the developers.
Gaming communities are riddled with messages complaining about the increasing number of cheaters ruining the game for players and the reputation of the developers.
At VB2019 in London, Kaspersky researcher Santiago Pontiroli described the many parallels between the challenges faced by the anti-malware industry and those faced by the anti-cheating industry. With most of the cheats heavily obfuscated and some exhibiting rootkit behaviours, Santiago believes this is an area in which the security industry needs to catch up.
Today we publish Santiago's paper in both HTML and PDF format, as well as the recording of his presentation in London.
 The cake is a lie! Uncovering the secret world of malware-like cheats in video games
The cake is a lie! Uncovering the secret world of malware-like cheats in video games
Have you carried out research that furthers our understanding of the threat landscape? Have you discovered a technique that helps in the analysis of malware? The Call for Papers for VB2020 in Dublin is open! Submit your abstract before 15 March for a chance to make it onto the programme of one of the most international threat intelligence conferences.