Posted by Martijn Grooten on Feb 22, 2019
The current generation of security professionals is probably more familiar with the way DNS works than they are with phone books, which are still often used as an analogy to explain DNS.
Domains play a crucial role in most cyber attacks, from the very advanced to the very mundane; being able to take down or block malicious domains is thus crucial. In a paper, co-written with Pawel Foremski and presented at VB2018 in Montreal, Farsight Security's Paul Vixie described the first systematic study of the lifetime of newly registered domains.
In particular, the study looked at how quickly newly registered domains became effectively dead, either because they had stopped resolving queries, or because all the relevant DNS blacklists had blocked them. Among the interesting results of the study is a great variation among the various top-level domains, as well as the fact that domains were generally blacklisted much faster than they were taken down.
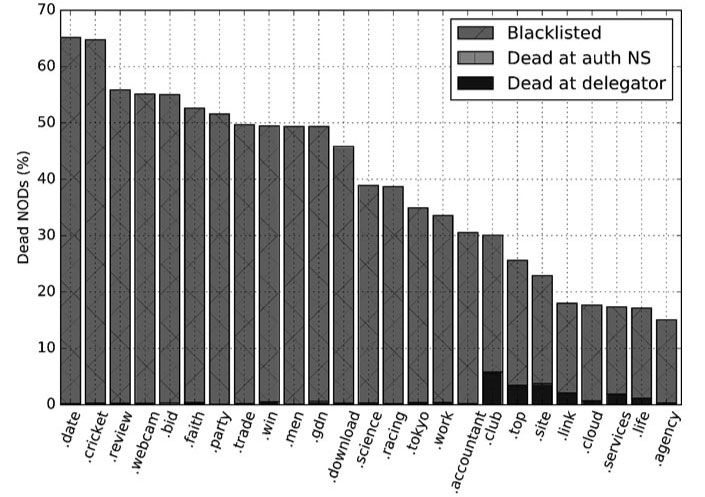 The rate and cause of death for the new gTLDs with the highest new domain death rates.
The rate and cause of death for the new gTLDs with the highest new domain death rates.
Today we have published the paper in both HTML and PDF format. We have also uploaded the video of Paul's presentation to our YouTube channel.
Have you carried out research that furthers our understanding of the threat landscape? Why not submit an abstract to VB2019, the 29th Virus Bulletin conference, which is to take place in London, 2-4 October 2019. The Call for Papers closes on 17 March.