Posted by Martijn Grooten on Aug 3, 2017
Damaging though they were, the recent WannaCry and (Not)Petya outbreaks taught security practitioners many valuable lessons. Unfortunately, they taught important lessons to malware authors too.
What contributed to the damage in both cases was the malware's ability to spread internally using a number of methods, most prominently (though in (Not)Petya's case not exclusively), a vulnerability in the SMB protocol that many organizations had failed to patch.
The authors of the 'TrickBot' banking trojan took note of this, and a new version of the malware, discovered by Deloitte researcher Luciano Martins and analysed by Flashpoint's Vital Kremez, suggests that they are experimenting with a module that uses SMB for lateral movement, though the module hasn't been fully implemented yet.
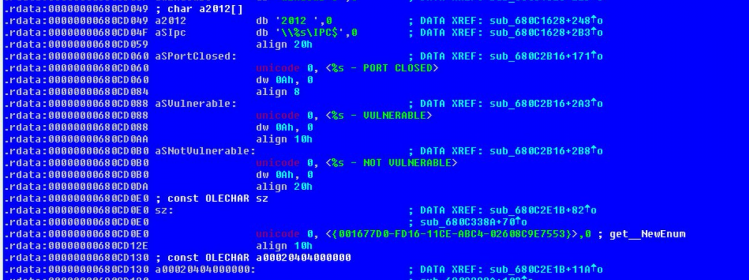
Trickbot's SMB implementation, as found by Luciano Martins.
Computer worms were a plague around the turn of the century, but thanks to improved security, the ubiquity of firewalls and the often overlooked benefits of NAT, malware that replicates fully automatically tends to be quite rare these days. But while the problem of malware spreading to other networks may have been mitigated pretty well, there are still many opportunities when it comes to malware spreading laterally within an organization.
For every method of lateral movement used by malware, there is probably a fairly easy way to prevent it; in the case of SMB that would be turning it off unless absolutely necessary, and in such cases always patching. But as malware authors shift their focus, it is likely that they will find many other ways to exploit the interconnectedness of computers within an organization. This won't be an easy problem to solve.
Of course, removing connections when they aren't needed could go a long way towards mitigating the damage, and there is a lot of value in network segmentation. But this approach isn't entirely painless. At VB, we have (touch wood!) never suffered from an attack that moved laterally within our networks. We have, however, spent quite a few frustrating hours having to find solutions to connections having become unavailable due to increased segmentation.
For more on recent changes to Trickbot, I recommend hasherezade's analysis at Malwarebytes's blog.
On the lessons learned from WannaCry that can be used for the common good, Razvan Gavrila from the EU's network agency ENISA will give a Small Talk at VB2017 in Madrid. Speaking of which, analyses of recent changes in malware would be excellent topics for last-minute papers – the call for last-minute papers closes on 3 September!