Posted by Martijn Grooten on Jan 24, 2017
"More malware is using cryptography, and more malware is using better cryptography," said Check Point researcher Yaniv Balmas on stage during VB2016. While the increased use of cryptography in general in recent years has been a great development, it is rather frustrating to find malware authors having joined the bandwagon – with ransomware being the ultimate example of cryptography being used maliciously.
But there is a silver lining, as highlighted by Balmas and his colleague Ben Herzog in their VB2016 paper 'Great Crypto Failures': crypto is hard to get right, and that goes for malware authors too. Furthermore, malware authors don't always have the luxury of being able to use a well-tested third-party library, as that would make their creations too bulky and easily detectable.
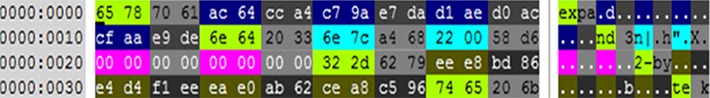
In their paper, which we publish today in both HTML and PDF format, Yaniv and Ben share some examples of crypto mistakes made by malware authors – which is not only a source for amusement, it also highlights the unique constraints under which malware authors operate.
We have also uploaded the video of our presentation to our YouTube channel.
Do talks like this inspire you to present your own research at one of the longest running and most international security conferences? Why not submit an abstract to the Call for Papers for VB2017, which will take place 4-6 October in Madrid, Spain.