Posted by Virus Bulletin on Aug 18, 2015
Products defy prediction of tougher circumstances.
When spam levels were recently reported to have dropped below 50% for the first time in 12 years, I wrote that it was 'not necessarily good news for spam filters': as spam filtering is almost entirely reactive, spam campaigns of smaller size are more likely to stay under the radar, which could have a detrimental effect on filters' performance.
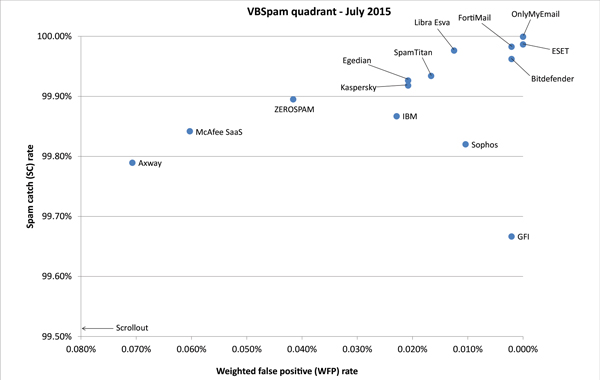
However, the latest set of VBSpam results suggest that, for now, there is little to worry about. After a sharp decline in spam catch rates in May, products' catch rates bounced back to an impressive average of 99.87% on this occasion.
But just as we warned against reading too much into this decline back in May, we continue to note that spam filter performance should be considered in a longer term view — which is why we run our VBSpam tests every second month. For now, however, it was nice to see products performing so well.
With false positive rates remaining relatively low, all but one of the 15 participating full solutions achieved a VBSpam award, and five of them — OnlyMyEmail, ESET, FortiMail, Bitdefender and GFI — earned a VBSpam+ award for blocking more than 99.5% of spam, while blocking no legitimate emails and very few newsletters.
The VBSpam summary report can be downloaded here in HTML-format or here as a PDF.
Are you providing an email security solution whose performance you'd like to be measured by Virus Bulletin? Email VB Editor Martijn Grooten at [email protected] or check out the details of our consulting services.
Posted on 18 August 2015 by Martijn Grooten