Posted by Virus Bulletin on Jan 6, 2015
Ahmed Zaki and Benjamin Humphrey describe a system they built for the automated detection of rootkit behaviour.
Since the close of the VB2014 conference in Seattle in October, we have been sharing VB2014 conference papers as well as video recordings of the presentations. Today, we have added ' Unveiling the kernel: rootkit discovery using selective automated kernel memory differencing', by Sophos researchers Ahmed Zaki and Benjamin Humphrey.
Whether you're responsible for IT security in a large corporation or work in an anti-virus vendor's lab, you are likely to have a system that automates the analysis of new malware samples. However, the very nature of rootkits makes them hard to classify (and in some cases even detect) using automated malware analysis techniques.
This is why Sophos researchers Ahmed Zaki and Benjamin Humphrey built a system that helps with the automated detection of rootkit behaviour.
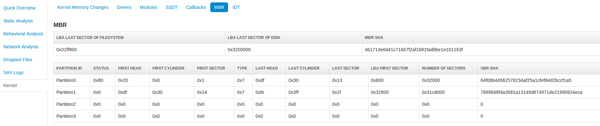
Their system makes use of the Cuckoo Sandbox, with the Sophos AV engine added to it. The latter has a presence in the kernel and can dump areas of kernel memory to a JSON file, which allows the system to show modifications made to the memory by the sample that is being analysed.
The paper explains in great detail how the system works, and then looks at a number of prevalent rootkits (TDL, Gapz, Turla and Necurs), for each of which the system was able to detect at least some of the rootkit behaviour. In the paper the authors also show how their system performed on sets of clean driver files and known malicious executables.
While the researchers say that their system is still very much a work in progress, it is great that they decided to share the details of a system they use internally with the VB2014 delegates. We are happy to share the details with an even wider audience by publishing the paper today.
You can read the paper here in HTML-format, or download it here as a PDF (no registration or subscription required). You can download the presentation slides here. We have also uploaded the presentation to our YouTube channel.
Those with a particular interest in rootkits and bootkits should read the VB2014 paper by Eugene Rodionov, Alexander Matrosov and David Harley which, among other things, looks at TDL and Gapz, and the three papers written by Peter Ferrie on Necurs: part 1, part 2, part 3.
Posted on 06 January 2015 by Martijn Grooten