Posted by Virus Bulletin on Jan 26, 2015
Thibault Reuille and Dhia Mahjoub use DNS data to look for clusters of malicious domains.
Since the close of the VB2014 conference in Seattle in October, we have been sharing VB2014 conference papers as well as video recordings of the presentations. Today, we have added 'Design to discover: security analytics with 3D visualization engine' by OpenDNS researchers Thibault Reuille and Dhia Mahjoub.
Our friends are at AV-Test and the USENIX conference - at least, those are the websites that, according to data from OpenDNS, people visiting www.virusbtn.com tend to visit as well.
The use of such DNS-based 'big data' doesn't just provide nice little nuggets of information though: in their VB2014 paper, Thibault Reuille and Dhia Mahjoub apply the same technique to command and control domains (typically using domain generation algorithms, or DGAs) for botnets.
In the paper, they study the domains used by the now defunct CryptoLocker ransomware and show how using only a few known DGA-domains as input, and without having to study the malware itself, they were able to find all the domains used.
In their presentation in Seattle, the researchers applied the same technique to both the old and the new versions of the notorious 'GameOver Zeus' botnet, which was taken down last year but which quickly resurfaced.
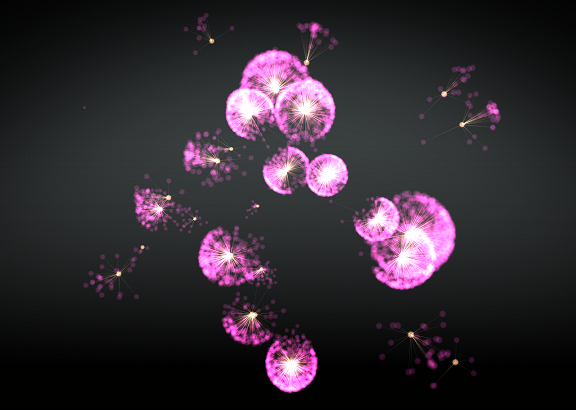
They were also able to visualise these patterns using a 3D framework which draws on both graph theory and particle physics. The framework they created is called OpenGraphiti and has been made available to other researchers.
You can read the paper here in HTML-format, or download it here as a PDF (no registration or subscription required). We have also uploaded the presentation to our YouTube channel.