Posted by Virus Bulletin on Sep 5, 2014
Hot topics to be covered at VB2014 conference in Seattle.
Although most of the VB2014 conference programme was announced back in April, it looks anything but dated. A paper on malicious ads became even more hot when java.com was found to serve such ads, while the recent data breach at Home Depot increased the relevance of a paper on point-of-sale malware.
Yet, as in previous years, we have set aside a section of the VB conference for 'last-minute' papers, the idea being that researchers submit proposals for these presentations very close to the conference itself, thus enabling them to cover topics that are as up-to-the-minute as possible.
The deadline for these papers closed last week and, less than three weeks before the conference, we are pleased to announce the seven selected papers that finalise the programme for VB2014.

The (in)security of the Internet of Things has become a major concern in recent years. Kaspersky researcher David Jacoby decided to try to find out if there is really a reason for concern by hacking devices in his own home. He will talk about his findings in his presentation 'How I hacked my own house!'.
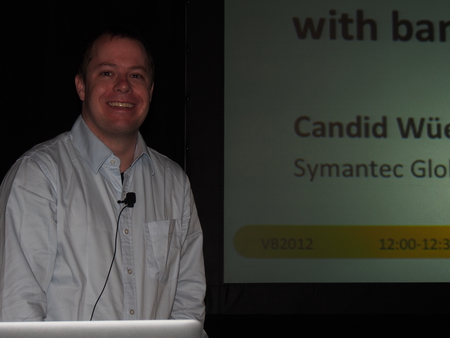
Perhaps even more worrying is the possible lack of security in devices that track or monitor one's health. In his presentation, 'Attack points in health apps & wearable devices - how safe is your quantified self?', Symantec's Candid Wüest will look at such devices and also demonstrate a proof-of-concept scanner that could track users of such devices without their knowledge.
It is not only innocent users that leak personal information through their online activities, though. Matt Bing, a researcher for Arbor Networks, found many open directories on botnet web servers in which he discovered new malware families, infection logs and unencrypted Bitcoin wallets. He will share details of his discoveries in his presentation 'Adventures in open directories'.
The presentation 'Back in BlackEnergy: 2014 targeted attacks in the Ukraine and Poland' from ESET researchers Robert Lipovsky and Anton Cherepanov is certainly 'hot'. In it, they will discuss the latest variants of the BlackEnergy trojan, which has undergone significant changes since its discovery in 2007, and which has spread by leveraging the geopolitical situation in Eastern Ukraine.
VB has a long history of hosting presentations that present tools that help with the detection and analysis of various kinds of bad activity. While working as an intern for Microsoft, together with his colleagues Steven Zhou and Geoff McDonald, Hexiang Hu developed a tool to automate the analysis of .NET malware. He will present the tool, as well as show how it was used to analyse the MSIL/Bladabindi backdoor in his presentation 'NET malware dynamic instrumentation for automated and manual analysis'.

Digging deep into possibly compromised systems, in his presentation 'Killing the rootkit - perfect physical memory process detection' IOActive's Shane Macaulay will show how, by identifying a system's page table, that it is possible to 'find everything' that could run on a system, to verify its integrity, thus allowing a researcher to detect rootkits.
Finally, digging one step deeper into a machine, one ends up at the BIOS, a part of a system often ignored by security software but unfortunately not by some advanced attackers. Xeno Kovah and his colleagues from The MITRE Corporation will show how to detect attacks at the BIOS level in their presentation 'Into the unknown: how to detect BIOS-level attackers'.
Between the keynote address and the closing panel there are 51 talks on the programme while there are also four excellent reserve papers lined up, should anyone have to cancel at the last-minute.
VB2014 is proving to be a very popular conference, but we have increased our capacity and registration is still possible. We also have some press places available for journalists wanting to attend. Please contact [email protected] if you want to apply for a press pass.
Posted on 05 September 2014 by Martijn Grooten