Virus Bulletin
Copyright © Virus Bulletin 2016
Rig, Angler, Nuclear, Magnitude. Few people outside security circles will have heard of them, yet they are behind what is possibly the worst large-scale malware plague ever: encryption ransomware. In particular, these are exploit kits which, when embedded into websites (often through compromised ads), check your browser for vulnerabilities and exploit them to push malicious software onto your computer.
Indeed, when, during our tests, we made requests to websites serving exploit kits, we found our test machines infected with ransomware such as Locky, Teslacrypt and Cerber, as well as other kinds of malware, including Bedep and Zbot variants. Many individuals and organizations have found themselves infected with malware in this way, and many have ended up paying hefty ransoms to attackers to get their files back.
Nuclear traffic followed by Locky traffic.
Patching remains a great way to reduce the chances of being infected, but in decades of IT security we've learned that users often don't do what's best for them or their employer. As a result, many organizations rely on web security products that run on the gateway and filter web content for malicious responses.
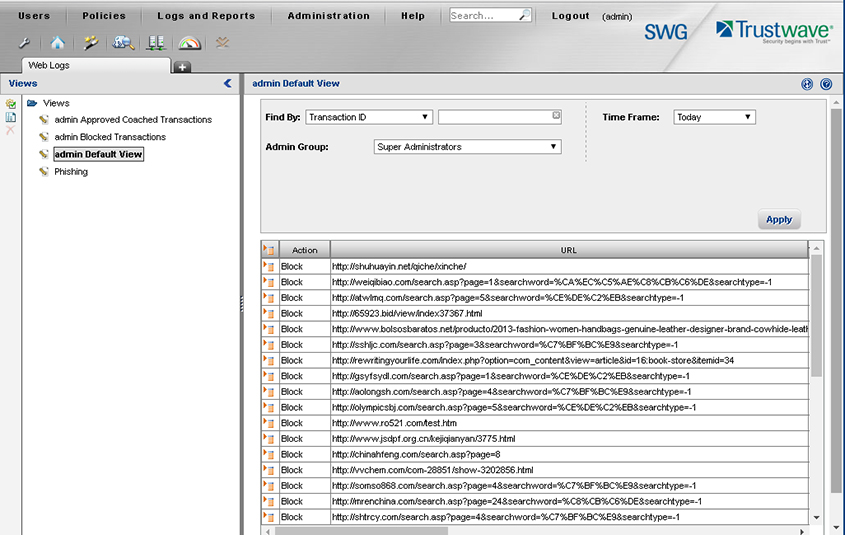
In Virus Bulletin's VBWeb tests we measure how effective products are at blocking malicious web traffic. In this report we focus on one particular product: Trustwave's Secure Web Gateway.
During the test period, which ran from 1 to 11 April 2016, we used a number of public sources, combined with the results of our own research, to open URLs that we had reason to believe could serve a malicious response in one of our test browsers, selected at random. When our systems deemed the response likely enough to fit one of various definitions of 'malicious', we made the same request in the same browser a number of times, each time with one of the participating products in front of it. The traffic to the filters was replayed from our cache. Note that we did not need to know at this point whether the response was actually malicious, meaning that our test didn't depend on instances already known to the industry or community. During the review of the corpus days later, we analysed the responses and only included cases in which the traffic was indeed malicious.
While we registered various types of malicious responses, including spam/scam sites and phishing pages, we decided to concentrate only on drive-by downloads, where the URL was an HTML page that forced the browser to download and/or install malware in the background. This is by far the biggest threat at the moment and makes unprotected web browsing more dangerous than ever.
In this test, we checked products against 439 cases, including 105 drive-by downloads (exploit kits) and 100 direct malware downloads that were all served in real time, while the malicious server was live. We also checked the product against 234 URLs that we call 'potentially malicious'. These are URLs for which we have strong evidence that they would serve a malicious response in some cases, but they didn't when we requested it. There could be a number of reasons for this, from server‑side randomness to our test lab being detected by anti-analysis tools.
The test focused on unencrypted HTTP traffic. It did not look at very targeted attacks or vulnerabilities in the products themselves.
We used two virtual machines, selected at random, from which to make requests. On each machine, an available browser was also selected at random.
We found that, in practice, we were far more likely to receive a malicious response for the Windows 7 machine using either version of Internet Explorer, hence most of the cases that ended up in the test used this configuration.
This machine had the following software installed:
The following browsers were installed:
This machine had the following software installed:
The following browsers were installed:
Drive-by download rate: 95.2%
Potentially malicious rate: 95.3%

Trustwave is one of the industry leaders when it comes to web security. Indeed, Trustwave's SpiderLabs blog is one of the resources we turn to for the latest research on exploit kits, so we were expecting the company's Secure Web Gateway product to do a very good job at blocking these threats.
We were not disappointed. The appliance, set up as an explicit proxy in our test lab, blocked more than 95 per cent of exploit kits – and did equally well at blocking potentially malicious URLs proactively. Given how quickly exploit kits change, and how difficult it is for organizations to make sure all endpoints are fully patched, this is a big deal.
There are many things users can and should do to mitigate drive-by downloads, patching being the most important. But for those organizations that cannot trust their users always to follow best security practice (which is probably all organizations), Trustwave's Secure Web Gateway removes 95 per cent of drive-by downloads. And that makes a huge difference.
Of course, Trustwave earns a very well deserved VBWeb award for its performance.
Trustwave: excellent protection.