In the run up to VB2016, we invited the conference sponsors to write guest posts for our blog. In the second of this series, ESET's Matías Porolli writes about malicious Visual Basic and JavaScript gaining prevalence in Brazil.
In the run up to VB2016, we invited the conference sponsors to write guest posts for our blog. In the second of this series, ESET's Matías Porolli writes about malicious Visual… https://www.virusbulletin.com/blog/2016/07/malicious-scripts-gaining-prevalence-brazil/
In 2001, ‘Code Red’ caused White House administrators to change the IP address of the official White House website, and even penetrated Microsoft’s own IIS servers.
Last week saw the 15th anniversary of the appearance of 'Code Red' (also known as 'Bady') - the first fileless worm, which spread by exploiting a vulnerability in Microsoft IIS,… https://www.virusbulletin.com/blog/2016/07/throwback-thursday-holding-bady/
Anti-virus vendor Avast has announced the acquisition of its rival AVG for 1.3 billion US dollars.
There was interesting news in the anti-virus world yesterday, as Avast announced the acquisition of its competitor AVG.
Both companies were founded in the Czech Republic and… https://www.virusbulletin.com/blog/2016/07/avast-acquires-avg-13bn/
Passwords have long been a weak point in the security chain, despite efforts to encourage users to pick strong ones. 13 years ago, Martin Overton wrote an article highlighting the weakness and explaining why it is the human element that presents the bigge…
A recent survey by mobile ID provider TeleSign revealed that 72% of security professionals believe that passwords will be phased out by 2025 - in favour of behavioural biometrics… https://www.virusbulletin.com/blog/2016/07/throwback-thursday-you-are-weakest-link-goodbye/
In a new paper published by Virus Bulletin, Sophos researcher Gabor Szappanos takes a look at the KeyBase keylogger, sold as a commercial product and popular among cybercriminals who use it in Office exploit kits.
Keyloggers have long been a popular tool for cybercriminals, something made worse by the fact that many of them are sold commercially.
Today, we publish a paper (here as a PDF)… https://www.virusbulletin.com/blog/2016/07/paper-new-keylogger-block/
VB2016, the 26th International Virus Bulletin conference, is an excellent reason to go to Denver, Colorado in the first week of October. But there is another reason to come to Denver: BSides Denver, which will take place the day after VB2016, on Saturday …
VB2016, the 26th International Virus Bulletin conference, is an excellent reason to visit Denver, Colorado in the first week of October this year. Of course, we are biased, but a… https://www.virusbulletin.com/blog/2016/06/bsides-denver-take-place-day-after-vb2016/
This week, well known and universally respected industry guru Mikko Hyppönen celebrates his 25th anniversary of working at F-Secure (formerly known as Data Fellows). VB takes a look back in the archives at two articles published in 1994: an "insight" into…
This week, well known and universally respected industry guru Mikko Hyppönen celebrates his 25th anniversary of working at F-Secure (formerly known as Data Fellows). In… https://www.virusbulletin.com/blog/2016/06/throwback-thursday-hypponen-data-fellow-finnish-sprayer/
Financial pressure can be a proactive and potentially very effective tool in making our computer ecosystems safer. By cleverly employing various trust metrics and technologies such as digital signing, watermarking, and public-key infrastructure in strateg…
Financial pressure can be a proactive and potentially very effective tool in making our computer ecosystems safer: making attackers spend real money before they can deploy malware… https://www.virusbulletin.com/blog/2016/06/economic-sanctions-malware/
In October 1994, a new multi-partite virus appeared, using some of the techniques developed by the Dark Avenger in Commander_Bomber. As if this were not enough, the One_Half virus could also encrypt vital parts of the fixed disk. Eugene Kaspersky provided…
The recently encountered Petya trojan comes as something of a blast from the past: it infects the Master Boot Record (MBR) and encrypts the Master File Table (MFT). Kaspersky… https://www.virusbulletin.com/blog/2016/05/throwback-thursday-one-half-lieutenant-commander/
 VB is excited to announce that, starting from the Q3 test, all VBSpam tests of email security products will be executed under the AMTSO framework.
VB is excited to announce that, starting from the Q3 test, all VBSpam tests of email security products will be executed under the AMTSO framework.
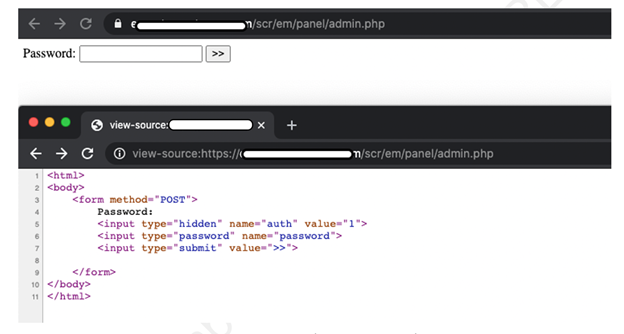
 In a new paper, researchers Aditya K Sood and Rohit Bansal provide details of a security vulnerability in the Nexus Android botnet C&C panel that was exploited in order to gather threat intelligence, and present a model of mobile AppInjects.
In a new paper, researchers Aditya K Sood and Rohit Bansal provide details of a security vulnerability in the Nexus Android botnet C&C panel that was exploited in order to gather threat intelligence, and present a model of mobile AppInjects.
 In a new paper, F5 researchers Aditya K Sood and Rohit Chaturvedi present a 360 analysis of Collector-stealer, a Russian-origin credential and information extractor.
In a new paper, F5 researchers Aditya K Sood and Rohit Chaturvedi present a 360 analysis of Collector-stealer, a Russian-origin credential and information extractor.
 VB has made all VB2021 localhost presentations available on the VB YouTube channel, so you can now watch - and share - any part of the conference freely and without registration.
VB has made all VB2021 localhost presentations available on the VB YouTube channel, so you can now watch - and share - any part of the conference freely and without registration.
 VB2021 localhost - VB's second virtual conference - took place last week, but you can still watch all the presentations.
VB2021 localhost - VB's second virtual conference - took place last week, but you can still watch all the presentations.
 The call for last-minute papers for VB2021 localhost is now open. Submit before 20 August to have your paper considered for one of the slots reserved for 'hot' research!
The call for last-minute papers for VB2021 localhost is now open. Submit before 20 August to have your paper considered for one of the slots reserved for 'hot' research!
 Kurt Natvig explains how he recompiled malicious VBA macro code to valid harmless Python 3.x code.
Kurt Natvig explains how he recompiled malicious VBA macro code to valid harmless Python 3.x code.
 In a new article, Aditya K Sood looks at the command-and-control (C&C) design of the AZORult malware, discussing his team's findings related to the C&C design and some security issues they identified.
In a new article, Aditya K Sood looks at the command-and-control (C&C) design of the AZORult malware, discussing his team's findings related to the C&C design and some security issues they identified.