Posted by on Oct 11, 2021
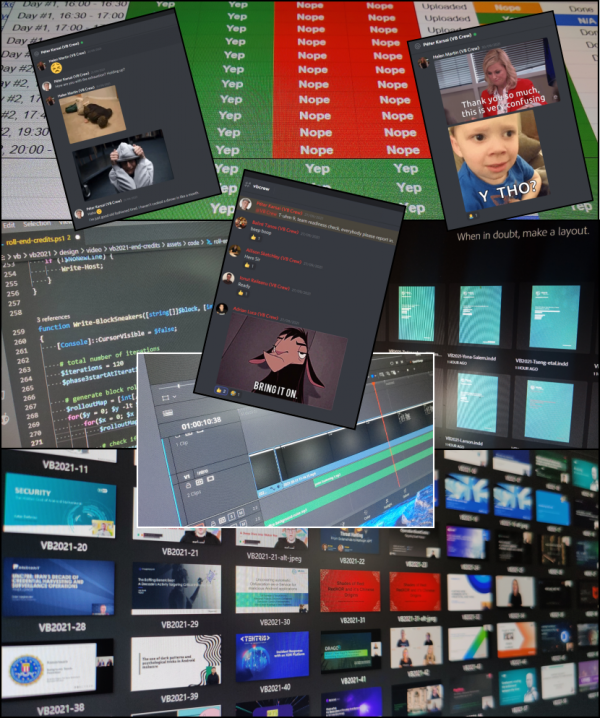
VB2021 localhost - VB's second virtual, and entirely free to attend VB conference - took place last week and was a great success.
If you missed it, don't worry, the content is still available to view.
You can rewind and watch the two live broadcasts, each of which features eight presentations and live Q&A with the speakers, and there are more than 30 presentations available in the on-demand library as well as 12 presentations in the Threat Intelligence Practitioners' Summit (TIPS), brought to you by our co-host the Cyber Threat Alliance.
All the content can now be viewed at https://vblocalhost.com/.
For those who tuned in last week, we would like to thank you all for coming along for the ride, as well as a huge thanks to all the speakers, partners, workshop hosts, the incredible tech team at Acorn AV and the wonderful host of the live show, Angela Lamont.