Posted by on Apr 2, 2020
The Middle East continues to be a hotbed of APT activity. The WindShift group is one of many APT groups active in the region. First described by Darkmatter’s Taha Karim in 2018, the group’s toolset includes malware for both Windows and macOS.
Building on that research, Jamf’s Patrick Wardle analysed the WindTail macOS malware used by the group in a paper presented at VB2019 in London. He analysed the use of custom URL schemes, which allowed for infection with minimal user interaction.
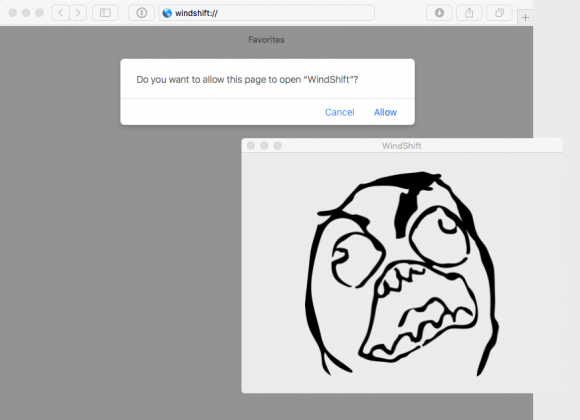 macOS launches the WindShift application.
macOS launches the WindShift application.
Patrick is a VB conference regular ─ he has spoken at every VB conference since 2014 ─ and has presented both offensive and defensive research on macOS attacks. In 2014, he presented on persistence methods for malware on macOS and in 2016 on secretly recording webcam streams.
Today, we publish Patrick's VB2019 paper in both HTML and PDF format and also release the recording of his presentation.
 Cyber espionage in the Middle East: unravelling OSX.WindTail
Cyber espionage in the Middle East: unravelling OSX.WindTail