Posted by Helen Martin on Apr 30, 2020
Web application vulnerabilities are an important entry vector for threat actors. Indeed, according to the 2019 Verizon Data Breach Incident Report, web applications, privilege misuse and miscellaneous errors account for 81 per cent of breaches of retail organizations.
In a paper presented at VB2019 in London, Prismo Systems researchers Abhishek Singh and Ramesh Mani discussed code injection vulnerabilities and presented a tool that could detect SQL, NoSQL and OS command injection exploitation.
Now, in a follow-up paper, Abhishek and Ramesh detail algorithms that can be used to detect SQL injection in stored procedures, persistent cross-site scripting (XSS), and server‑side request forgery (SSRF) by instrumenting web applications.
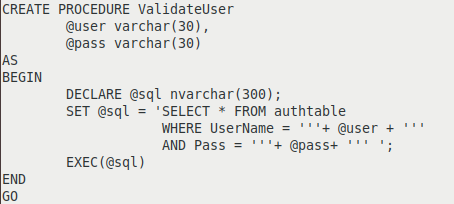 Example of stored procedure prone to SQL injection.
Example of stored procedure prone to SQL injection.
You can read both papers in both HTML and PDF format:
 New paper: Detection of vulnerabilities in web applications by validating parameter integrity and data flow graphs
New paper: Detection of vulnerabilities in web applications by validating parameter integrity and data flow graphs
 VB2019 paper: Catch me if you can: detection of injection exploitation by validating query and API integrity
VB2019 paper: Catch me if you can: detection of injection exploitation by validating query and API integrity