Posted by on Mar 20, 2020
It is one of the worst things on the Internet: child sexual abuse material (CSAM), sometimes referred to as ‘child porn’. Many misconceptions exist around CSAM, one of which is that it is only ever accessed from home. In fact, many company networks are used to download and store CSAM, often unbeknownst to network administrators.
In a paper presented at VB2019 in London, NetClean’s Richard Matti and Anna Creutz looked at this problem. They described the problem and what companies can do to detect CSAM on their internal networks, to clean it up, with the ultimate goal of safeguarding children.
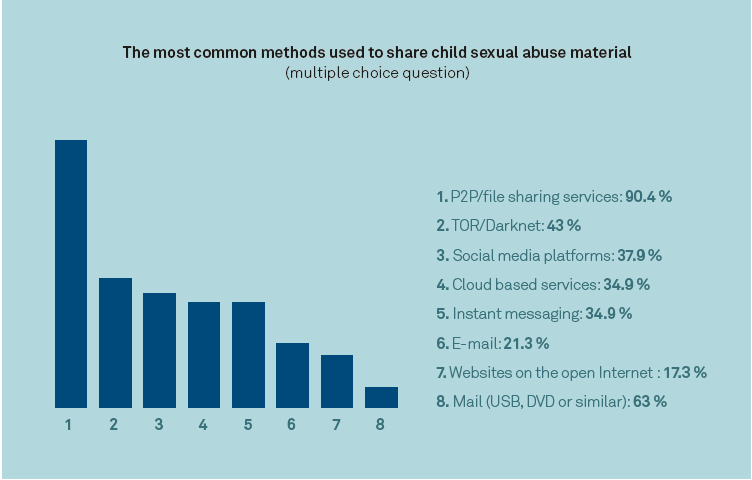 The most common methods used to share child sexual abuse material.
The most common methods used to share child sexual abuse material.
Today, we publish Richard and Anna's paper in both HTML and PDF format.
 Why companies need to focus on a problem they do not know they have
Why companies need to focus on a problem they do not know they have