Posted by on Mar 24, 2020
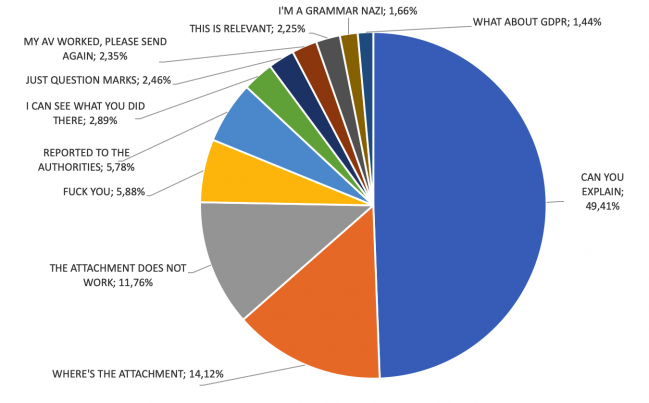
In an illuminating study – possible thanks to a unique perspective on a malicious email campagin – cybercrime journalist and researcher Adam Haertlé (BadCyber.com/ZaufanaTrzeciaStrona.pl) read, analysed and classified 1,976 responses sent by victims of a malicious email campaign.
In taking revenge for Adam having written about them on his blog, the senders of a malicious email campaign decided to include his email address in the ‘reply-to’ field of the emails – thus meaning that Adam was privy to all replies sent in response to their campaign.
Many of the victims were unaware that the message they had received was fake and contained malware. Some even asked for the (malicious) attachment to be resent as it had been blocked by their anti-virus product.
 Message analysis.
Message analysis.
At VB2019 Adam presented an analysis of the unsolicited responses – revealing that the we should not count on users to react properly to Internet threats.
Today we publish Adam's paper in both HTML and PDF format and also release the recording of his presentation.
 2,000 reactions to a malware attack – accidental study
2,000 reactions to a malware attack – accidental study