Posted by Martijn Grooten on Nov 29, 2019
Having returned from its summer break, Emotet is once again being used as the first stage of many often prominent and costly malware infections. A detailed analysis of the malware was given in a paper presented at VB2019 by Sophos researcher Luca Nagy.
But Emotet isn't just a very clever piece of malware. It also uses very clever techniques to evade email security products – something we have noticed many times in our lab.
One such technique is the hijacking of existing email threads, which makes it harder to filter the emails and makes recipients more likely to think the emails are legitimate. This thread hijacking was the subject of a last-minute paper presented at VB2019 by ZEROSPAM researchers Pierre-Luc Vaudry and Olivier Coutu, who also explained how clustering helped them detect such campaigns.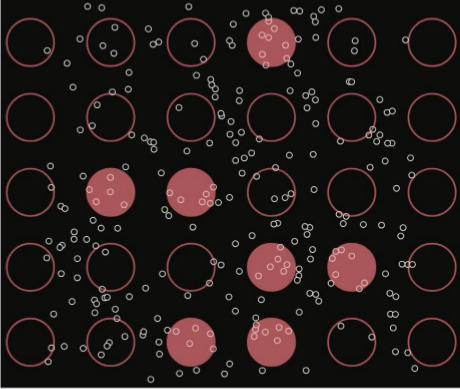
Today, we have uploaded the video of Pierre-Luc and Olivier's talk in London to our YouTube channel.