Posted by Martijn Grooten on Sep 3, 2019
Those who attend security conferences know the importance of 'hallcon': the conversations that take place in the corridors in between sessions or sometimes between people who have sneaked out of the talks. Hallcon has long been an important part of the Virus Bulletin Conference and four years ago we formalised this by setting up a room for "Small Talks".
Small Talks are sessions that last longer than the usual 30 minutes and are held in a smaller room that is more suitable for discussion and interactive sessions.
This year's programme contains five Small Talks ─ with the room also being used for a number of other activities, more on which soon.
The first Small Talk is something anyone interested in the history of malware should attend. Sophos researcher Andrew Brandt will lead a 60-minute session on running and analysing some of the oldest known malware ─ something that may be more helpful for those fighting today's threats than it may at first seem (a point also made in another presentation).
Virus Bulletin has a long history of testing security products, a subject that has regularly featured at the VB Conference too. But the testing of products also happens within many larger organisations. In a Small Talk, John Hawes and Dennis Batchelder of the Anti-Malware Testing Standards Organization will discuss the subject and describe how the work done by AMTSO may be helpful here.
A very important, yet often forgotten aspect of computer security is the use of technology to facilitate stalking and domestic abuse. We had Joseph Cox talk about stalkerware at VB2017 and this issue is now the subject of a Small Talk led by Vyacheslav Zakorzhevsky from Kaspersky and Rachel G. of the National Network to End Domestic Violence. Together with the audience they will discuss how tech can help to address the domestic violence issue.
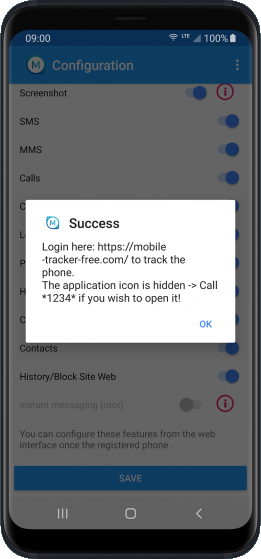
Example of stalkerware being installed on a phone. Source: Kaspersky.
As security experts, we are focused on the confidentiality, integrity, and availability of our data and systems, yet we often fail to consider the equivalent for people ─ forgetting that people are the most crucial part of any security set-up. In an interactive Small Talk, Jamie Tomasello of Duo Security will reflect on availability and burnout, and propose ways in which we can do things better.
Finally, the High Tech Crime Team of the Dutch police will host a session on the work they do (which will also be the topic of a presentation on Wednesday) and discuss how the malware research community can collaborate with them and other law enforcement agencies.
Have you already booked your ticket for VB2019? Don't forget to register to join us in London, 2-4 October!