Posted by Martijn Grooten on Dec 12, 2018
The APT-C-23 group, which targets users in the Middle East and in particular in the State of Palestine, was named and first reported on by 360 in a Chinese language blog post in early 2013. Its campaigns have since been written about by many security vendors, including Palo Alto and Cisco Talos.
Check Point reported a renewed attack by the group in the summer of this year, and it was Check Point researcher Aseel Kayal who gave a last-minute presentation on the campaign at VB2018 in Montreal.
In her presentation, she explained the modus operandi of the group and its habit of making references to various TV shows, including US sitcom The Big Bang Theory. And, in the spirit of industry cooperation that we so like to encourage at the conference, she also connected the various dots from the other vendors' reports on this threat actor.
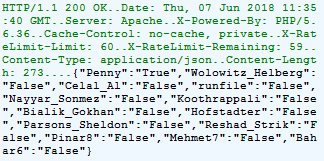 APT-C-23 C&C communication, with references to modules named after TV characters. (Source: Check Point.)
APT-C-23 C&C communication, with references to modules named after TV characters. (Source: Check Point.)
We have now uploaded the video of Aseel's talk to our YouTube channel so you can see what she had to say for yourself.