Posted by Martijn Grooten on Dec 7, 2018
The leaking or publishing of malware source code often leads to multiple spin-off families based on the code. Never has this been more clear than in the case of the Mirai Internet of Things (IoT) botnet. Mirai made its name when it was used in some damaging DDoS attacks in the second half of 2016; the source code was leaked shortly afterwards.
At VB2018 in Montreal, Ya Liu from Qihoo's 360 Netlab team – which has published a lot of research on Mirai and its descendants – presented a paper that he co-wrote with his colleague Hui Wang on Mirai variants. In the paper, the researchers described how they extract various data from Mirai samples and how this can then be used to classify and track variants of the botnet.
Mirai variants remain a hot topic among botnet researchers, and several talks at this week's Botconf 2018 conference looked at these malware families, including one by Ya Liu, who discussed the same research as he presented at VB2018 in Montreal.
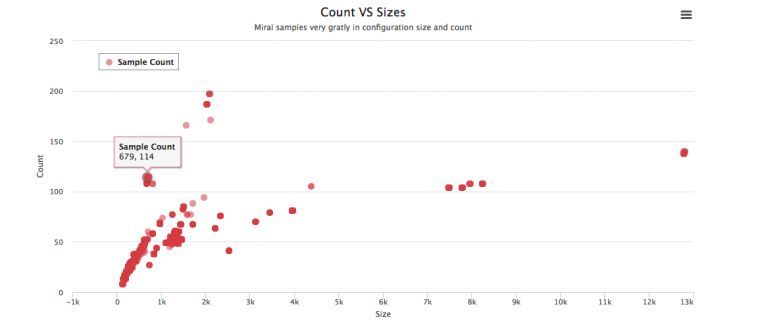 Clustering samples based on configuration count and size.
Clustering samples based on configuration count and size.
Today, we publish Ya and Hui's VB2018 paper in both HTML and PDF format.