Posted by Martijn Grooten on Dec 14, 2018
A large portion of today's malware infections use malicious Office documents as a first-stage payload. Typically, the user is tricked into enabling macros or disabling some security protection, after which the next-stage payload is downloaded and executed.
However, a different kind of Office malware targets outdated versions of Microsoft Office, which continue to be widely used. These files are usually generated using an exploit builder. Analogous to exploit kits targeting web users, such builders attempt to exploit a number of vulnerabilities, hoping that at least one will work.
One of several active exploit builders is Threadkit. Sold on the cybercrminal underground for US$800, it was first reported on by Proofpoint in March of this year. Threadkit is the most prevalent exploit builder at the moment, and is utilised in about a third of such attacks. It has been used in some intensive campaigns to deliver the notorious Trickbot malware.
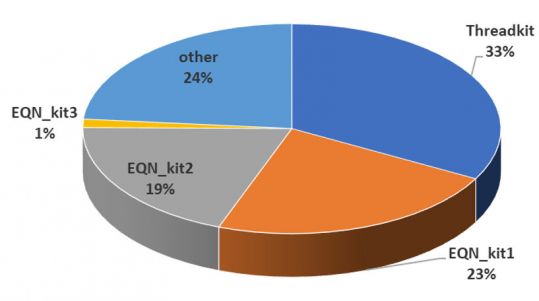 Exploit builder utilisation in attacks, from Gábor Szappanos's VB2018 paper.
Exploit builder utilisation in attacks, from Gábor Szappanos's VB2018 paper.
New research by Fidelis (pdf) has looked at a new version of Threadkit that has been used by the 'Cobalt' group. This prominent cybercrime group, also known as 'Carbanak', has targeted banks in Eastern Europe and has become active again despite the arrest of its alleged mastermind earlier this year.
At VB2018 in Montreal this year, Sophos researcher Gábor Szappanos presented a paper on Office exploit builders in which he provided a detailed overview of all the active builders. The paper looked in particular at CVE-2017-0199, one of the vulnerabilities often exploited by this kind of malware; it was also used in the latest Threadkit campaign.
Gábor has long studied such builders; he discussed them in a paper presented at VB2017 last year, when he also won the Péter Szőr award for previously published research on the now disappeared AKbuilder (pdf).
Today, we have published Gábor's VB2018 paper in both HTML and PDF format. We have also uploaded the video of his presentation to our YouTube channel.