Posted by Martijn Grooten on Dec 4, 2018
The Necurs botnet has been active for some time. In 2014, Virus Bulletin published a 3-part article by Peter Ferrie (1, 2, 3) who had studied the botnet in great detail. And although, as is typical for botnets, Necurs' activities can be somewhat volatile, it has been used for some notorious and malicious spam campaigns in recent years.
Earlier this year, I wrote about how the Flawed Ammyy remote access trojan (RAT) was being pushed to some more interesting Necurs-infected devices, and I also mentioned that the same RAT had been spread by a Necurs-spam campaign. This particular campaign was analysed by Avast researchers Jan Sirmer and Adolf Streda, who delivered a last-minute presentation about it at VB2018.
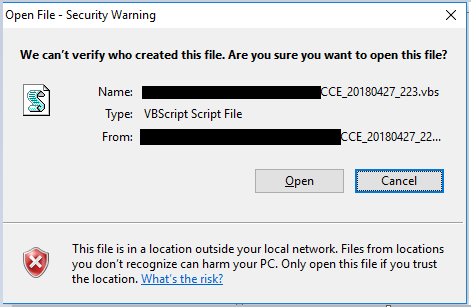 Script run directly from remote storage.
Script run directly from remote storage.
Jan and Adolf have written a paper for VB describing the branch of Necurs they have been monitoring, the changes it has undergone in the course of a year, and presenting an analysis of Flawed Ammy. You can read the paper in both HTML and PDF format.
We have also uploaded the video of their VB2018 presentation to our YouTube channel.
This week, Jan and Adolf will speak once again about their research at Botconf in Toulouse, France. As in previous years, members of the Virus Bulletin will be attending Botconf.