Posted by Martijn Grooten on Aug 28, 2018
Shout 'blockchain' in a group of security experts and everyone will start to laugh. It is fair to say that the security community tends to be rather sceptical about cryptocurrencies and blockchains and the promises that come with them.
But it is easy to forget that many well-meaning people invest real money in these technologies. And that the technologies are often actually very interesting.
One such technology is Ethereum, a blockchain-based platform that offers smart contract functionality. In a VB2018 paper on this technology, MRG Effitas researcher Zoltan Balazs describes in simple terms how the technology works – and it is indeed promising.
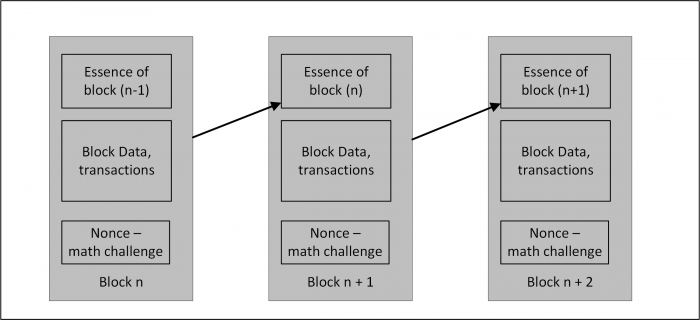 Blockchain, high level overview.
Blockchain, high level overview.
However, he then goes on to describe a number of security issues inherent to Ethereum and how these have led to various high-profile and often very costly hacks, leading to the conclusion that designing smart contracts is hard. To quote Zoltan: "Everyone can come up with a design he or she is not able to hack, but this doesn't mean it is not hackable."
Zoltan's presentation is just one of many great reasons to come to VB2018 (2-4 October in Montreal). Check out the programme for full details of what else is on the agenda - book your ticket now for what promises to be a memorable event!
And don't forget, if you have some (hot) research to share, the call for last-minute papers remains open until 2 September.