Posted by Martijn Grooten on Aug 15, 2018
"Understanding the new paradigm", Malwarebytes researcher Jérôme Segura writes in the title of his upcoming VB2018 presentation on drive-by mining. He could hardly have put it more accurately – the rise of malicious cryptocurrency miners is the main security trend of the past 12 months.
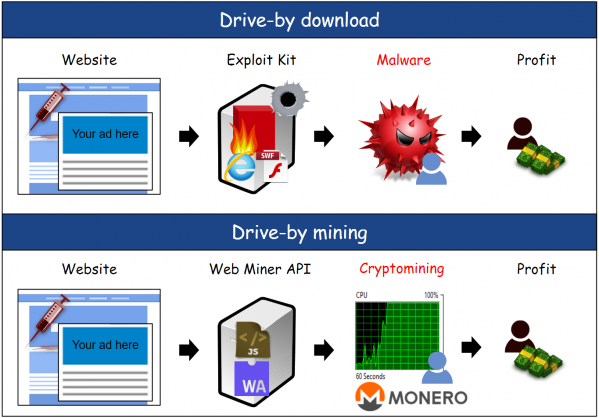
In the paper, Jérôme will look at those miners that run in the browser, often (though not always) without the user's permission (hence the term "drive-by mining"). The paper not only looks at how this kind of mining works, but also puts it in the context of a decline in exploit kits and the rise of Monero, a cryptocurrency well suited for in-browser mining.
Jérôme, who has spoken at Virus Bulletin conferences several times before, is one of the leading experts on exploit kits (his quarterly overviews are a must-read for anyone following this type of threat) and we very much look forward to him providing the audience with a well-informed overview of this very important development.
Jérôme's presentation is just one of many great reasons to come to VB2018 (2-4 October in Montreal). Check out the speaker page for details of other leading experts presenting at the event, and check out the programme for full details of what else is on the agenda - book your ticket now for what promises to be a memorable event!
And don't forget, if you have some (hot) research to share, the call for last-minute papers remains open until 2 September.