Posted by Martijn Grooten on May 4, 2017
Anyone who has ever investigated a malware or phishing attack will know the feeling: "if only I could find out what IP address this domain pointed to when the attack took place". If you're tasked with performing incident response in your organisation, collecting passive DNS data is probably a good idea.
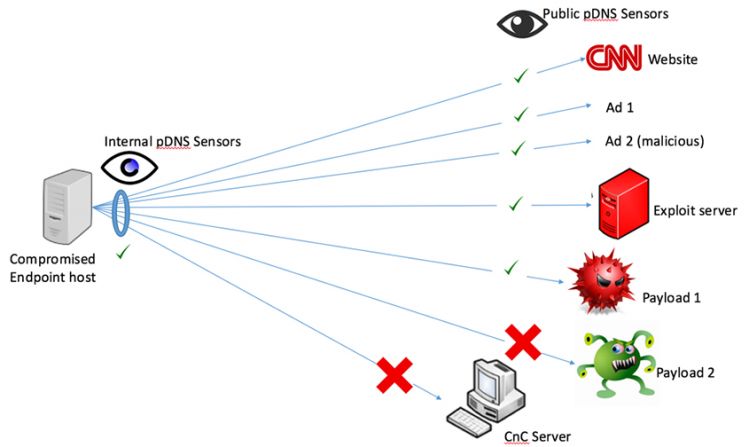
One way to do this is by using the free PassiveDNS Splunk app. At VB2016 in Denver, Splunk researchers and authors of the app Kathy Wang and Steve Brant presented this app, explained how it was built and how it could be used. Their paper is now available to read (HTML and PDF) on our website, and the video of their presentation is available to view on our YouTube channel.
If you're interested in what can be done with such data, make sure you come to VB2017 and watch OpenDNS researchers Dhia Mahjoub and David Rodriguez present their paper "Beyond lexical and PDNS: using signals on graphs to uncover online threats at scale".
VB2017 will take place in Madrid, 4-6 October 2017. Register now for an Early Bird discount!