Posted by Martijn Grooten on Nov 28, 2017
A well-known security researcher once said: "if you purposely choose Android you are either Poor, Cheap, or really hate Apple."
Android has a bad reputation in security circles, though these days that is less because of a lack of effort on Google's part and more because of the prevalence of many older devices with unpatched vulnerabilities.
It is easy to make this problem seem bigger than it is. The typical Android vulnerability still requires an app to be installed which, on non-rooted devices, means that the app first needs to get onto Google Play – this is something that malware manages to do, quite regularly, and sometimes with a worryingly large number of downloads.
However, the prevalence of such Android malware is still small compared to that of Windows malware and may, for the average home user, not justify the cost of a new phone.
For users with a more advanced threat model, things are different though. A good example of this is 'Tizi', a backdoor family discovered by researchers from Google, which used various apps found on Google Play. The malware used one of nine vulnerabilities, all patched between 2013 and 2015, to obtain root on a device which was then used to record calls, siphon out messages, and access personal information.
It is unclear what kinds of users were targeted by this malware, but interestingly, some 80% of installations were found in Kenya, once again highlighting that malware is a truly global problem. (Those who attended Tyrus Kamau's VB2017 talk "The state of security in Africa: Kenya" will, of course, not be surprised by this.)
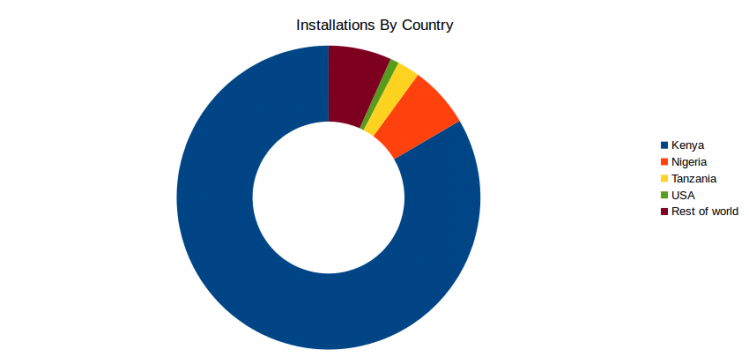
Tizi installations by country. Source: Google.
Targeted malware attacks are certainly not limited to powerful intelligence agencies, and victims may be targeted for political, business and sometimes very personal reasons, as the widespread use of spyware in domestic abuse cases shows. For such potential victims, using a phone that will receive security patches is an important first step in their digital defence.
Finally, Google deserves credit for taking down this malware and for implicitly admitting that its efforts to keep Google Play malware-free are not 100% successful. That too, is an important first step.