Posted by Martijn Grooten on Aug 22, 2017
We all know that security often gets in the way of convenience, but sometimes security even gets in the way of security. This is the case, for example, when a decision needs to be made on whether to break an encrypted HTTP connection in order to inspect it for malicious content.
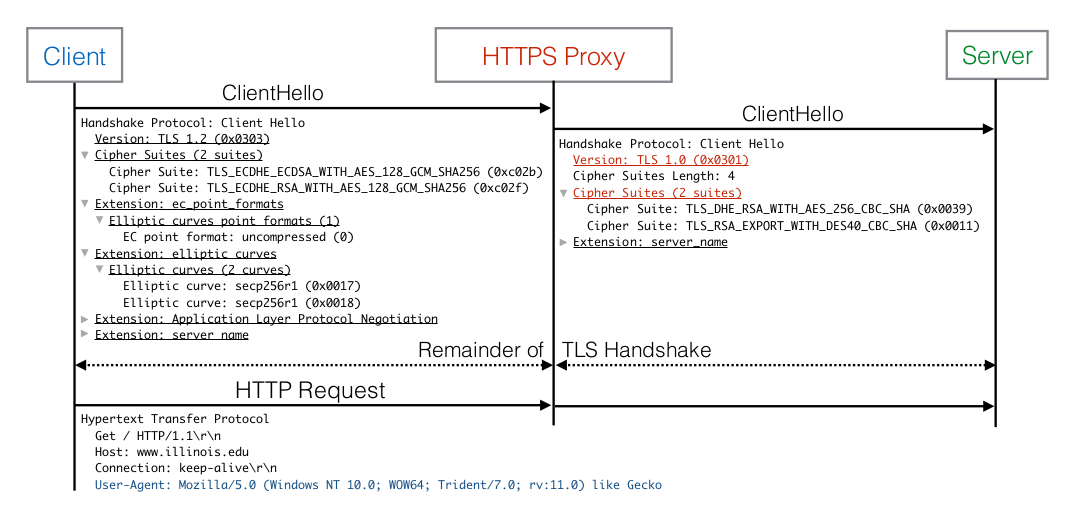
HTTPS allows for this to happen neatly and transparently so that, as long as you trust the intercepting product, the security of the connection is not degraded. Unfortunately, a recent paper shows that many such products implement HTTPS poorly and thereby significantly increase the attack surface – a rather embarrassing fact given that it concerns security products.
Aware of the importance of this issue for security vendors, many of whom will be in attendance at VB2017, we have asked Cloudflare's Nick Sullivan to give a Small Talk on this topic at the conference in Madrid. Nick is one of the world's leading experts on encryption in general, and HTTPS in particular, and was one of the authors of the aforementioned paper. At VB2014, he presented a paper on DNSSEC.
To make sure you don't miss out on this important discussion, as well as the rest of the packed conference programme, book your VB2017 ticket now!
And don't forget that the call for last-minute papers, dealing with hot security research, is open until 3 September.