Posted by Martijn Grooten on Sep 15, 2016
"Don't roll your own crypto", software developers are often told: cryptography is hard and thus it is always safer to use a well-tested public library rather than writing your own implementation.
Not everyone heeds that advice though, and among those not listening are the developers of various malware families. In a paper to be presented at VB2016, Check Point researchers Ben Herzog and Yaniv Balmas will look at a number of interesting and sometimes humorous examples of unfortunate cryptographic implementations, including, but not limited to, various ransomware families.
However, the paper isn't just about making fun of the mistakes made by those on the wrong side. Ben and Yaniv explain how malware authors are under unique constraints which often prevent them from including public cryptography libraries: doing so would make their creations too bulky and easy to detect.
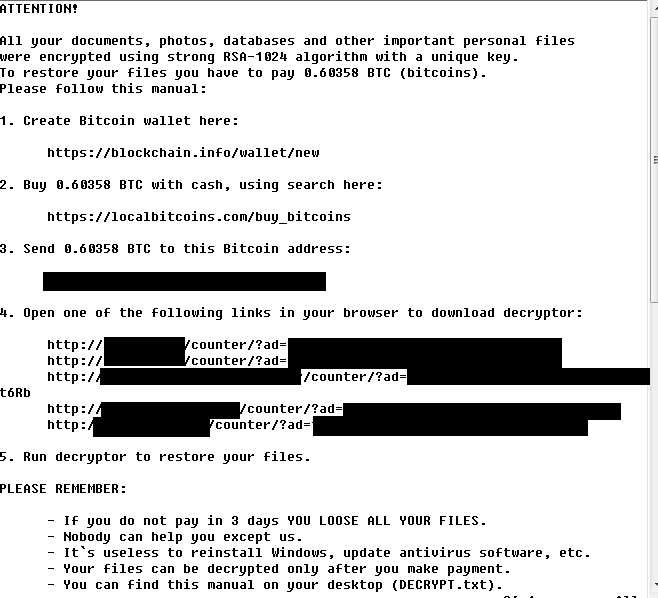
In the particular case of ransomware, the mistakes made are often essential for researchers who want to write decryption tools. In a last-minute paper, Malwarebytes researcher hasherezade will talk about her often successful attempts to 'crack' a number of recent ransomware variants.
VB2016 takes place at the Hyatt Regency Hotel in Denver 5-7 October. Why not register and come along to hear not only these but more than 50 other presentations on hot security topics as well.
