Posted by Martijn Grooten on Sep 1, 2016
The recent discovery of a one-million-device IoT botnet used for DDoS attacks should be ample proof that concerns over the security of the Internet of Things are not merely theoretical.
 Unfortunately, the use of specific components and the wide variety among them makes reverse engineering such devices rather complicated. But it doesn't need to be, Fortinet researcher Axelle Apvrille found, as most of these devices come with a 'backdoor': a corresponding mobile app.
Unfortunately, the use of specific components and the wide variety among them makes reverse engineering such devices rather complicated. But it doesn't need to be, Fortinet researcher Axelle Apvrille found, as most of these devices come with a 'backdoor': a corresponding mobile app.
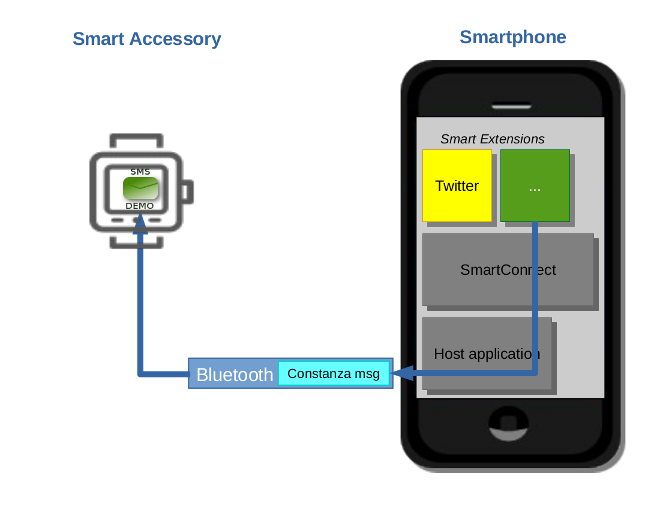
Reverse engineering this app, which can be done using off-the-shelf reverse-engineering software, can be an essential first step in understanding the architecture of the device. In the paper 'Mobile Applications: a Backdoor into Internet of Things?', which Axelle will present at VB2016 in Denver, Axelle shows how this works by way of three examples: a watch, an alarm and a toothbrush, all of which come with an Internet connection.
To hear Axelle and other world-class security researchers present their research, why not register for VB2016? Or, if you have done research of your own into whether a device is as 'smart' as its manufacture claims it is, why not submit a last-minute paper abstract? The call for papers closes on Sunday 4th September.