Posted by Martijn Grooten on Sep 6, 2016
While man-in-the-middle attacks are relatively rare (especially among those not attending hacker conferences), it is quite common for computer users to be in a situation where an attacker could have an opportunity to take control of their network traffic. There are, of course, network mechanisms that seriously mitigate the risk, such as VPN or HTTPS, but these aren't universally applied and can sometimes be bypassed through social engineering.
 So how do you know that your network traffic is being modified? At VB2016, Cylance researcher Brian Wallace will present a multi-platform tool that runs on the endpoint and detects (active) man-in-the-middle attacks.
So how do you know that your network traffic is being modified? At VB2016, Cylance researcher Brian Wallace will present a multi-platform tool that runs on the endpoint and detects (active) man-in-the-middle attacks.
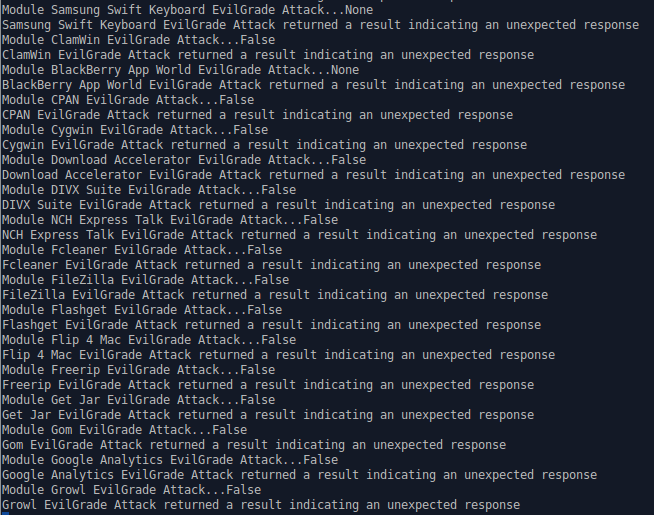
Dubbed 'MITM Canary', the tool achieves this in two different ways. Firstly, it makes network requests and compares the responses in various ways with the expected response; a difference could indicate something is modifying network traffic. Secondly, it attempts to identify the methods used to launch MITM attacks, such as controlling DNS responses.
At around the time of his conference presentation, Brian will release the tool and its source code to the public.
Last year, Brian wrote two technical articles for Virus Bulletin: on the use of .NET GUIDs to find malware and on an optimization for ssDeep to make it work at scale. Both are well worth a read, especially if you are into Big Data research.
Registration for VB2016 is still open.
