Posted by Martijn Grooten on Sep 12, 2016
Though still well behind that of Windows malware, the prevalence of malware targeting OS X has increased in the past year to the point where Mac users can't assume they are safe just because of the operation system they are using. The question of how to effectively detect new Mac malware is one that is becoming increasingly important for the security community.
Today, we publish a paper (also as pdf) by Vincent Van Mieghem, a former student at Delft University of Technology, who introduces a novel way of detecting malware running on OS X.
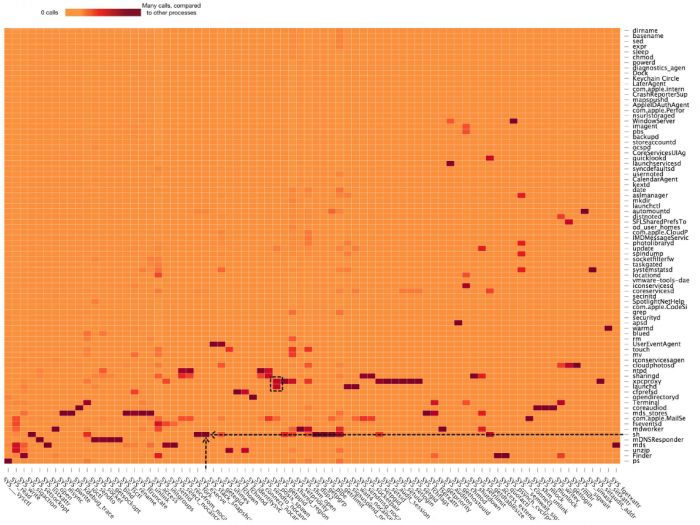
Vincent looked at patterns among the system calls used by known malware samples, and compared these to the calls used by legitimate software. This helped him to find patterns in the system calls that would be indicative of malicious behaviour.
He used this technique against a set of newly discovered malware samples and found a 100% detection rate. He also looked at false positives and found that it varied from 0% for typical users to 20% for 'power users' (who tend to use many developer tools, which often exhibit behaviours that are less easy to distinguish from those of malware).
The research was done as part of Vincent's Master's thesis, which he wrote during an internship at Fox-IT. (Vincent currently works for PwC Cybersecurity.)
The increasing prevalence of OS X malware is also reflected in the VB2016 programme, which includes several papers on the subject. Registration for the conference is still open - have you registered yet?