Posted by Martijn Grooten on Jul 20, 2016
Anti-detection techniques are almost as old as malware itself and have developed well beyond hash busting techniques. As security products adapt their detection tools, malware authors need to find new ways to prevent their malware from being blocked while it is running.
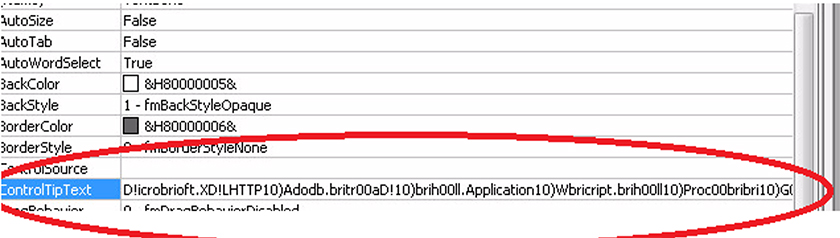
In a new paper (also available as PDF) published today by Virus Bulletin, FireEye researcher Ankit Anubhav looks at a number of such techniques that were found in recent malware samples, from hiding malicious code called by Office macros in form fields to renaming the Windows StartUp folder to maintain persistence in a less obvious way.