Posted by on Jul 15, 2016
In the run up to VB2016, we invited the conference sponsors to write guest posts for our blog. In the first of this series, ESET writes about the SBDH toolkit.
Over the course of the last year, ESET has detected and analysed several instances of malware used for targeted espionage – dubbed the SBDH toolkit. Using powerful filters, various methods of communication with its operators, and an interesting persistence technique, it aims to exfiltrate selected files from governmental and public institutions, most of which are focused on economic growth and cooperation in Central and Eastern Europe.

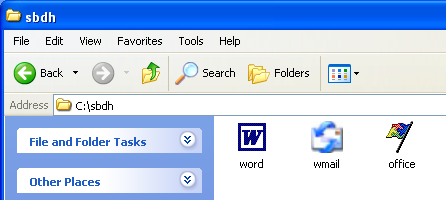
The attackers spread a double-extension executable via a phishing email and using real Microsoft application icons to make it look more legitimate.
Once executed, the malware connects to a server and downloads a backdoor and a data stealer. These are used to control the compromised machine remotely and to exfiltrate the data, respectively. This campaign also counts on powerful filters in order to extract specific information.
The toolkit implements multiple custom-made substitutive methods for communication with its C&C server, as well as an interesting way of locating an alternative C&C server in case the original is unavailable.
The SBDH espionage toolkit reminds us that even advanced threats are still being spread via traditional vectors, and underlines the importance of having properly trained staff along with multi-layered security solutions to prevent these threats.
SBDH findings were presented during the Copenhagen Cybercrime Conference 2016 by ESET researchers Tomáš Gardoň and Robert Lipovský. You can find the full article at WeLiveSecurity.com. More articles from the ESET experts can be found on the latest research section of their blog.
A few VB2016 sponsorship opportunities are still available, including some that offer a speaking slot on the programme. If you are interested in becoming a sponsor of VB2016, please contact [email protected].