Posted by on Jun 13, 2016
Recently, a new trend has emerged in non-Windows DDoS attacks. Malware has evolved into complex and relatively sophisticated pieces of code, employing compression, advanced encryption and even rootkit capabilities. Machines running systems supporting the ELF format are targeted – meaning that anything from desktops and servers to IoT devices such as routers or digital video recorders (DVRs) are at risk.
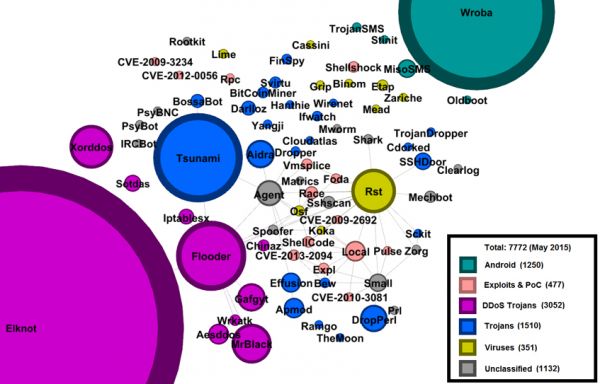 The ELF malware space.
The ELF malware space.
In their VB2015 paper, Peter Kálnai and Jaromír Hořejší look at the current state of DDoS trojans forming covert botnets on unsuspecting systems. The paper provides a technical analysis of the most important malware families, focusing on infection methods, dynamic behaviour, C&C communication, obfuscation techniques, advanced methods of persistence and stealth, and elimination of rivals.
In their paper Peter and Jaromír look at the cybercriminals' behaviour and introduce their operation tools, including vulnerability scanners, brute-forcers, bot builders and C&C panels. They also discuss methods and techniques and the targets of these attacks.
Read the paper here in HTML format or here as a PDF, and find the video on our YouTube channel, or embedded below.