Posted by Martijn Grooten on Apr 22, 2016
Given the sheer volume of new malware samples discovered every day, security researchers eagerly make use of tools that will help automate their research and analysis.
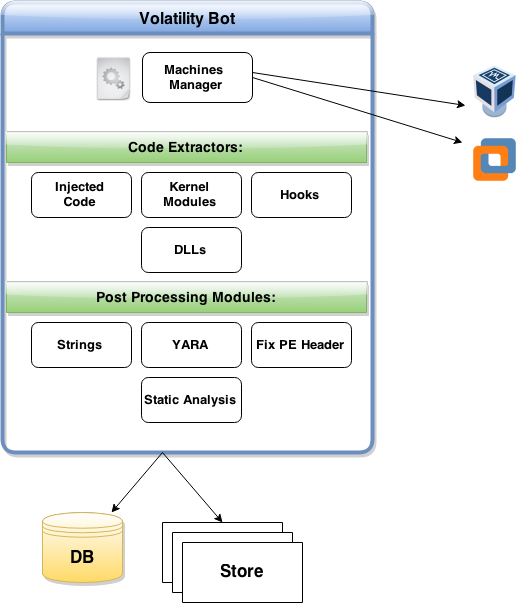
IBM Trusteer researcher Martin Korman wrote one such tool, 'VolatilyBot', which extracts malicious code from packed binaries, leveraging the functionality of the Volatility Framework. At VB2015 in Prague, Martin presented his tool and the paper he wrote describing it.
You can read his paper "VolatilityBot: Malicious Code Extraction Made by and for Security Researchers" here in HTML format or here as a PDF, and find the video on our YouTube channel, or embedded below.
Are you interested in presenting your research at the upcoming Virus Bulletin conference (VB2016), in Denver 5-7 October 2016? The call for papers is now open.