Posted by Virus Bulletin on Nov 3, 2015
Thorough analysis of this new kid on the malware block.
Times are changing rapidly for banking trojans. Some prominent arrests and at least partially successful takedowns have left space for new criminal entrepreneurs in this malicious, yet highly profitable market. 'Shifu' seems to have filled part of this space.
First mentioned publicly by IBM in late August, Shifu (Japanese for 'thief') was found to target 14 Japanese banks, though it has the potential to attack other banks too.
Today, we publish a paper by Fortinet researchers Floser Bacurio Jr and Wayne Low, who analysed a recent sample of Shifu.
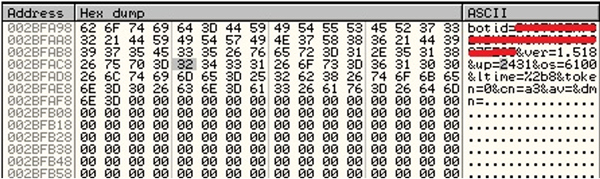
From the dropper, via various techniques used to frustrate automated and manual analysis, to the ways in which the malware steals banking credentials and other private data and can even destroy itself and the operating system it runs on: Floser and Wayne take the reader step by step through the malware, making this an essential read for anyone having to deal with Shifu infections.
Shifu has taken many leaves out of other banking trojans' books, making it not the most groundbreaking piece of malware. Moreover, the reliance of this sample's dropper on CVE-2015-0003 (patched in February 2015) for privilege escalation could make it less of a threat for fully up-to-date systems. Still, for many people Shifu is a serious threat and it may well stick around for some time.
You can read the article here in HTML format or download it here as a PDF.
Posted on 03 November 2015 by Martijn Grooten