Posted by Virus Bulletin on Aug 26, 2015
Raul Alvarez performs low-level analysis of information-stealing trojan.
The Gamker information-stealing trojan (also known as Shiz) has been around for a few years. It made the news back in 2013 when it was found to target SAP applications.
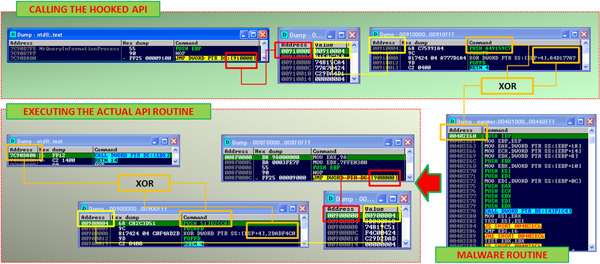
Today, we publish an article by Fortinet researcher Raul Alvarez who performed a low-level analysis of the trojan, in which he focused on its code injection and API-hooking routines.
You can read the article here in HTML format or download it here as a PDF.
If you enjoy this kind of low-level malware analysis, make sure to check out previous articles Raul has written for VB, including analyses of Vawtrak and Neshta.
Posted on 26 August 2015 by Martijn Grooten