Posted by Virus Bulletin on Jun 26, 2015
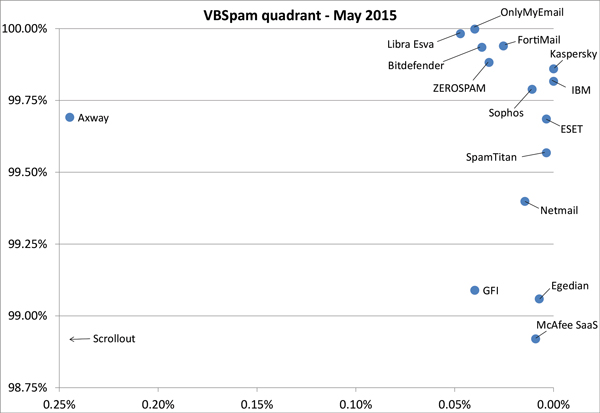
Despite a drop in catch rates, 15 products earn a VBSpam award, with four earning a VBSpam+ award.
Spam is notoriously volatile and thus, while we like to make the news headlines with our tests as much as anyone, we would warn against reading too much into the fact that the percentage of spam missed by spam filters almost doubled in the most recent VBSpam test.
In the test, which ran for 16 days in April and May, filters missed an average of 0.4% of emails — up from 0.18% in February. Though these numbers might not appear all that worrying, very low delivery rates are part of spammers' business models. With a lot of spam containing or linking to malware, lower catch rates aren't just a nuisance.
Nevertheless, despite the lower catch rates, most products continued to do a good job of mitigating the spam problem. Fifteen out of 16 products achieved a VBSpam award in this test and four of them — Kaspersky, IBM, ESET and SpamTitan — achieved a VBSpam+ award for blocking more than 99.5% of spam, while blocking no legitimate emails and very few newsletters.
The full VBSpam report can be downloaded here in HTML-format or here as a PDF.
Are you providing an email security solution whose performance you'd like to be measured by Virus Bulletin? Do not hesitate to email VB Editor Martijn Grooten at [email protected] or check out the details of our consulting services.
Posted on 26 June 2015 by Martijn Grooten