Posted by Virus Bulletin on Apr 2, 2015
Hong Kei Chan and Liang Huang describe the various aspects and the evolution of point-of-sale malware.
Since the close of the VB2014 conference in Seattle in October, we have been sharing VB2014 conference papers as well as video recordings of the presentations. Today, we have added 'Swipe away, we're watching you' by Fortinet researchers Hong Kei Chan and Liang Huang.
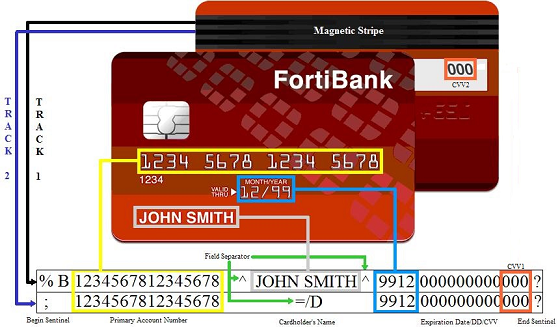
Point-of-Sale (PoS) malware was a little known threat until late 2013. Since then, a large number of US chain stores have suffered data breaches via their payment terminals.
In their VB2014 paper, Hong Kei Chan and Liang Huang first present a bird's-eye view of PoS malware, after which they look at one particular variant: Dexter. During their presentation, they gave a live demonstration of how the PoS malware siphoned out credit card data to a command and control server.
You can read the paper here in HTML-format, or download it here as a PDF (no registration or subscription required). You can download the presentation slides here. We have also uploaded the presentation to our YouTube channel.
PoS malware continues to be a problem. Once again, VB2015 will feature a presentation on the subject, this time by iSIGHT Partners researcher Ken Dunham. Registration for VB2015 will open soon.
Posted on 02 April 2015 by Martijn Grooten