Posted by Virus Bulletin on Apr 16, 2015
Users do choose weak passwords, but they aren't as big a problem as we think.
This week, I spent a few days at the Cyber Security Summit Financial Services conference in Prague, discussing the state of security with people who work in the financial sector.
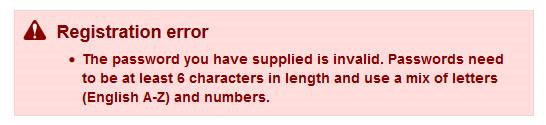
Unsurprisingly, a common topic of discussion was that group of individuals who cause headaches for all security engineers: users. They show a surprising inventiveness when it comes to doing things wrong and are often willing to go so far as to take a photograph of their list of TAN codes to help crooks circumvent two-factor authentication. On top of that, they have a tendency to choose very weak passwords.
But does the latter actually matter? Leading a discussion among the audience, I asked whether it would introduce a significant risk if I were to choose the simple password 'Prague' for my online banking. Someone working in security at a large bank said that, while he had seen many cases of financial fraud and theft, he had never seen a case where a weak password was an issue. Others in the room confirmed this.
Indeed, any decent online banking system allows a very limited number of 'guesses' when attempting to log in, thus meaning that only the most obvious password choices ('password', '123456' or one's surname) will give an attacker a reasonable chance of getting in. And even if an attacker does get in, two-factor authentication should prevent them from doing any actual harm.
Banking malware has become pretty inventive at bypassing two-factor authentication — and users are often willing to provide a helping hand. But password security doesn't make a difference here: entering a password on a phishing site is no safer if the password is strong.
When we talk about the ease of cracking passwords, we consider the second-to-worst case scenario where an adversary gets hold of a file of passwords, hashed using a single iteration of MD5 without the use of salt. (Ironically, in the worst case scenario, where an adversary gets hold of a file of plain text passwords, the strength of these passwords is irrelevant.)
It is mostly this scenario that makes us tell people to choose strong passwords — as we should continue to do. But in reality, using slow hashing algorithms combined with a salt is increasingly common. Moreover, an adversary who is so deep into a bank's system they can obtain the password file, is likely to be able to do so much harm that it makes the strength of all passwords yet again irrelevant.
Security professionals have a tendency to suggest the state of security is really bad. In many cases this is indeed the case. But the problem with password security isn't as big a problem as it is often suggested.