Posted by Virus Bulletin on Nov 11, 2014
Five initial victims of infamous worm named.
Today, as Wired journalist Kim Zetter publishes her book Countdown to Zero Day on Stuxnet, researchers from Kaspersky and Symantec published blog posts that shine a light on how the malware spread to its likely target, the Natanz plant in Iran, and to hundreds of thousands of other computers.
Earlier stories had suggested that Stuxnet had somehow escaped from the plant, but because Stuxnet conveniently keeps a breadcrumb log that tracks how the worm has spreaded thus far, Symantec researcher Liam O'Murchu was able to conclude that all infections originated outside the Natanz plant.
A blog post by Kapsersky researchers explains how it came that the malware still spread so widely.
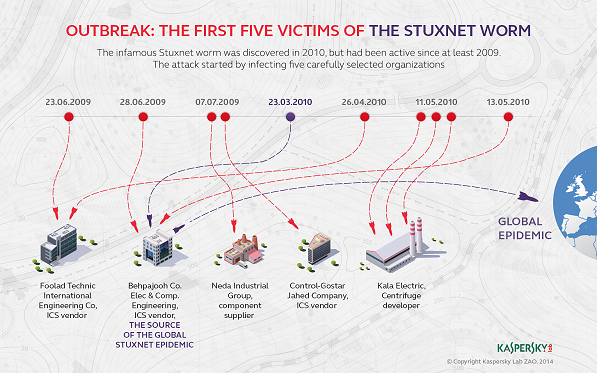
The infection started at five different companies and organisations in Iran, now named by Kaspersky and all closely linked to the country's nuclear program. This helped Stuxnet reach the systems at its ultimate target, which was no trivial task, given that these systems weren't connected to the Internet.
However, errors and design flaws caused the worm to spread from one of targeted companies, Behpajooh Co, to a large number of computers inside and outside Iran. It was this spreading that led to Stuxnet's discovery in the summer of 2010.
Stuxnet famously was the subject of two presentations during VB2010, that saw several global affairs journalists cross the ocean to attend the conference and even led to coverage at the BBC.
Unfortunately, in 2010 we didn't record conference presentations, but Mikko Hyppönen (F-Secure) recorded Liam O'Murchu's demonstration on how Stuxnet's SCADA component was able to make centrifuges spin faster than intended. He demonstrated this by writing a program that blew up a balloon and then writing malicious code that modified the program so that it would continue to pump air into the balloon making it eventually explode.
A review of Countdown to Zero Day will appear on this website later this month.
Posted on 11 November 2014 by Martijn Grooten