Posted by Virus Bulletin on Nov 19, 2014
Kerberos bug means one set of credentials suffices to rule them all.
If you are a Windows systems administrator, the content of this blog post will (hopefully) not come as a surprise. If it does, you should finish reading it quickly and make some time to apply the out-of-band patch MS14-068 to all Windows systems under your control as soon as possible.
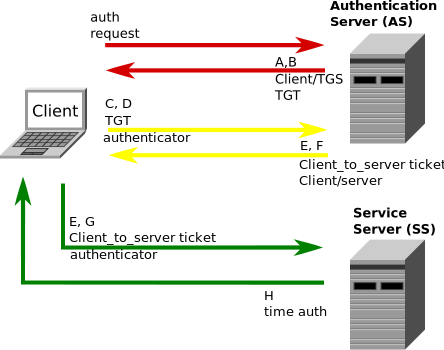
The patch fixes CVE-2014-6324, a checksum vulnerability in the Kerberos authentication protocol. It means that anyone with a user account on a local domain could elevate privileges to those of the domain administrator account.
The vulnerability has been rated 'critical', the highest possible severity rating, which is uncommon for privilege escalation vulnerabilities. However, the rating appears to be justified, as the vulnerability can be exploited remotely. It means that an attacker targeting an organization's network only needs to get hold of one valid set of credentials to take full control of the domain.
Indeed, Microsoft reports that the bug has already been exploited in targeted attacks in the wild.
MS14-068 means an intern can get access to the CEO's office by holding his thumb over the photo on his ID-card. While working from home.— Martijn Grooten (@martijn_grooten) November 18, 2014
In a blog post giving more details on the vulnerability, Microsoft engineer Joe Bialek advises that domain controllers running Windows Server 2008R2 and below should be given the highest priority, but says that all Windows versions should be fixed as soon as possible.
Should a domain already have been compromised, the only way for this to be remediated is a complete rebuild of the domain.
Posted on 19 November 2014 by Martijn Grooten