Posted by Virus Bulletin on Oct 15, 2014
Surprisingly, the presence of more URLs doesn't necessarily make spam easier to block.
Yet again, we have good news for those who need to run a spam filter (in other words: everyone who runs a mail server). 15 of the full solutions participating in our comparative anti-spam tests achieved a VBSpam award. They all blocked a large percentage of spam, while blocking very few legitimate emails. Only one product (the open source solution Scrollout F1) failed to achieve such an award this time.
Seven of the products - Bitdefender, ESET, GFI, Libra Esva, Mailshell, Netmail Secure, OnlyMyEmail and ZEROSPAM - achieved a VBSpam+ award for blocking more than 99.5% of spam, while generating no false positives at all in the 'ham' corpus, and very few false positives in a separate corpus of newsletters.
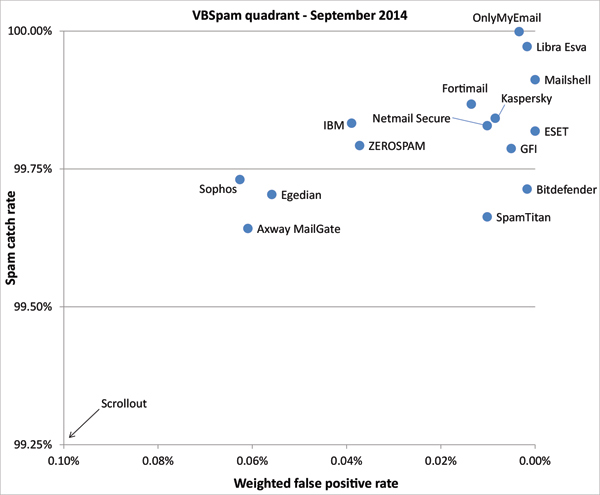
Compared to the last test, most products saw an increase in their spam catch rates, showing that the decrease we saw then was temporary. Of course, spam is a problem of volume, so while the catch rates are pretty high, you shouldn't expect anything less from your email security solution.
This month, we also looked at a possible correlation between the number of domains present in spam and the likeliness of such an email being blocked. After all, many spam filters make use of URL- or domain-based blocklists, and spammers are known to use compromised domains or URL shorteners to prevent their emails from being caught out this way.
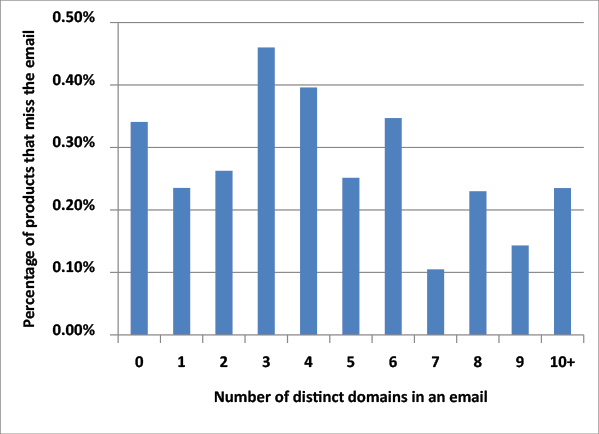
Somewhat surprisingly, on this month's spam feed we didn't notice such a correlation. This is a likely consequence of the fact that spam filters use a combination of many tools to determine whether an email is spam; hence one single factor, though contributing, does not necessarily have an impact that can be measured.
Again, this month's report has been split in two. A summary of the results with a focus on the state of spam can be viewed here in HTML format, or downloaded here as a PDF. The full report, with performance details of all participating products, can be viewed here in HTML format, or downloaded here as a PDF.
As of this summer, all content published through Virus Bulletin is available free of charge, and the test reviews are no exception. We encourage readers to make use of this and read the full report, if not for the performance details of the various products, then at least for the 'state of spam' overview these bi-monthly reports provide.
Posted on 15 October 2014 by Martijn Grooten