Posted by Virus Bulletin on Aug 4, 2014
RAT gets instructions from Yahoo Mail address.
One of the big challenges for malicious actors in operating a RAT (remote administration tool) is how to control the malware and retrieve data gathered from the infected machine. Listening on a certain port, or regularly connecting to a remote server, is behaviour that is likely to be spotted by intrusion detection systems.
Malware authors have become rather inventive in their efforts to control malware stealthily. 'Miniduke', for instance, used specially created Twitter accounts to retrieve command and control URLs.
Today, we publish a paper by Paul Rascagnères, a researcher for German security firm G Data, in which he analyses a new RAT called IcoScript - which, until recently, had gone undetected since 2012.
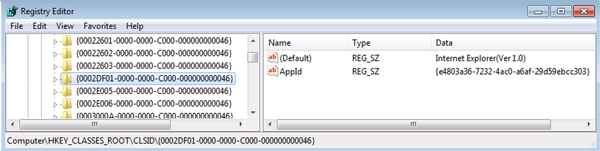
The malware uses the Component Object Model technology in Microsoft Windows in order to get Internet Explorer to make HTTP requests to remote services. It also uses its own kind of scripting language to perform tasks.
What makes IcoScript unique is the fact that it connects to a Yahoo Mail account controlled by its authors to receive instructions - which are stored in specially crafted emails in the inbox. Access to webmail services is rarely blocked in corporate environments and the traffic is very unlikely to be considered suspicious.
Moreover, the modular nature of the malware makes it very easy for the attackers to switch to another webmail service, such as Gmail, or even to use services like Facebook or LinkedIn to control the malware while running a low risk of the communication being blocked.
The paper can be downloaded here in HTML format or here as a PDF.
If you are interested in stealthy techniques employed by malware, I recommend you read Paul's interesting analysis of the 'Poweliks' malware that resides in the Windows registry.
Posted on 04 August 2014 by Martijn Grooten