Posted by Virus Bulletin on Jul 30, 2014
Flexible module-handling mechanism allows malware to adjust functionalities at will.
The history of the 'Bflient' worm goes back to the discovery of its first variants in June 2010. The malware was created using the 'ButterFly Flooder' toolkit, which is an update to 'ButterFly Bot' - made (in)famous because it was used to create the Mariposa botnet.
Today, we publish a paper by Meng Su and Dong Xie, two researchers from Fortinet, who studied recent variants of Bflient.
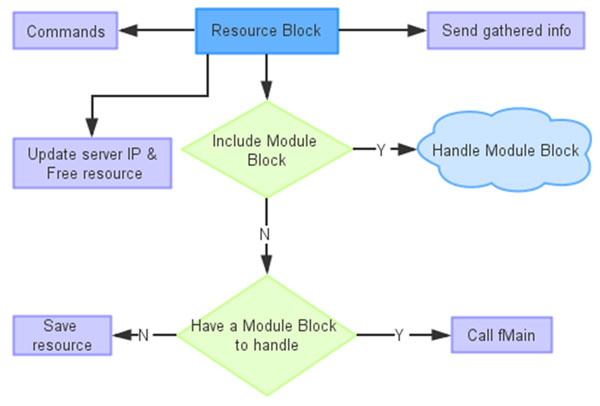
In the paper, Meng and Dong dig deep into the malware: from anti-analysis tricks used in the packer and during initialization, to the worm's ability to download 'resource blocks' from the command and control server. This modular architecture gives a lot of flexibility to the malware authors. A number of resource blocks are hard coded in the malware; these handle, for instance, the displaying of advertisements on infected PCs, downloading other pieces of malware, or the spreading of the worm via removable devices.
The paper can be downloaded here in HTML format or here as a PDF. If you are interested in this kind of malware analysis, you will find plenty of that in our archive, which has been made freely available. Among them are two other papers co-written by Dong Xie: one on Zortob and one on KakaoTalk.
Posted on 30 July 2014 by Martijn Grooten