Posted by Virus Bulletin on Jun 23, 2014
Automatic analysis of malicious payloads becomes a little bit harder again.
A security researcher at ESET has discovered how a malicious site serving the Angler exploit kit prevents automatic analysis by making a user click a link before being redirected to the exploit kit.
Having spent many hours during the past two years building a framework for Virus Bulletin's soon-to-be-launched web filter tests, I know that being served malicious content from the web isn't as easy as it may seem, especially if you want it to happen automatically.
Although people commonly speak of 'malicious URLs', in fact the response returned (and in many cases whether this response is malicious) depends on the IP address the request was made from, the time the request was made, the browser used, and the headers sent.
And, as I pointed out in my VB2012 presentation, in some cases a malicious response is only given when a user interacts in a particular way. A few years ago, for example, we learned that the Nuclear exploit kit required a user to move their mouse before being redirected to the malicious payload.
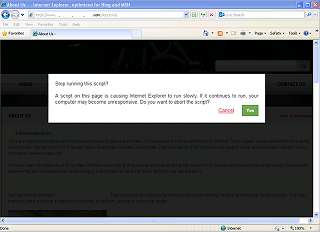
As Sébastien Duquette found, a website serving the Angler exploit kit requires the user to click a link before being redirected to the actual exploit kit. To entice them into clicking the link, they are presented with an alert about a script that causes the browser to run slowly. Regardless of whether the user clicks 'Yes' or 'Cancel', they are redirected to the malicious payload.
The purpose of this seems clear: preventing automatic analysis of the malicious payload. However, in this particular case, Sébastien found the keys to the castle: he realised that the final payload was available XOR-encrypted with a fixed keystream, allowing him to find the payload URL without having to click the link.
The fight between exploit developers and security firms is one of the many cat-and-mouse games the security community is involved in. In this case, the mice are going to great lengths to prevent the cats from noticing their presence.
The video recording of my VB2012 presentation has now been uploaded to YouTube.
Update this blog was updated on 23 June to reflect the fact that the redirect is not part of Angler itself. Thanks to Sébastien Duquette for pointing this out.